
Security News
Risky Biz Podcast: Making Reachability Analysis Work in Real-World Codebases
This episode explores the hard problem of reachability analysis, from static analysis limits to handling dynamic languages and massive dependency trees.


Sarah Gooding
July 18, 2025
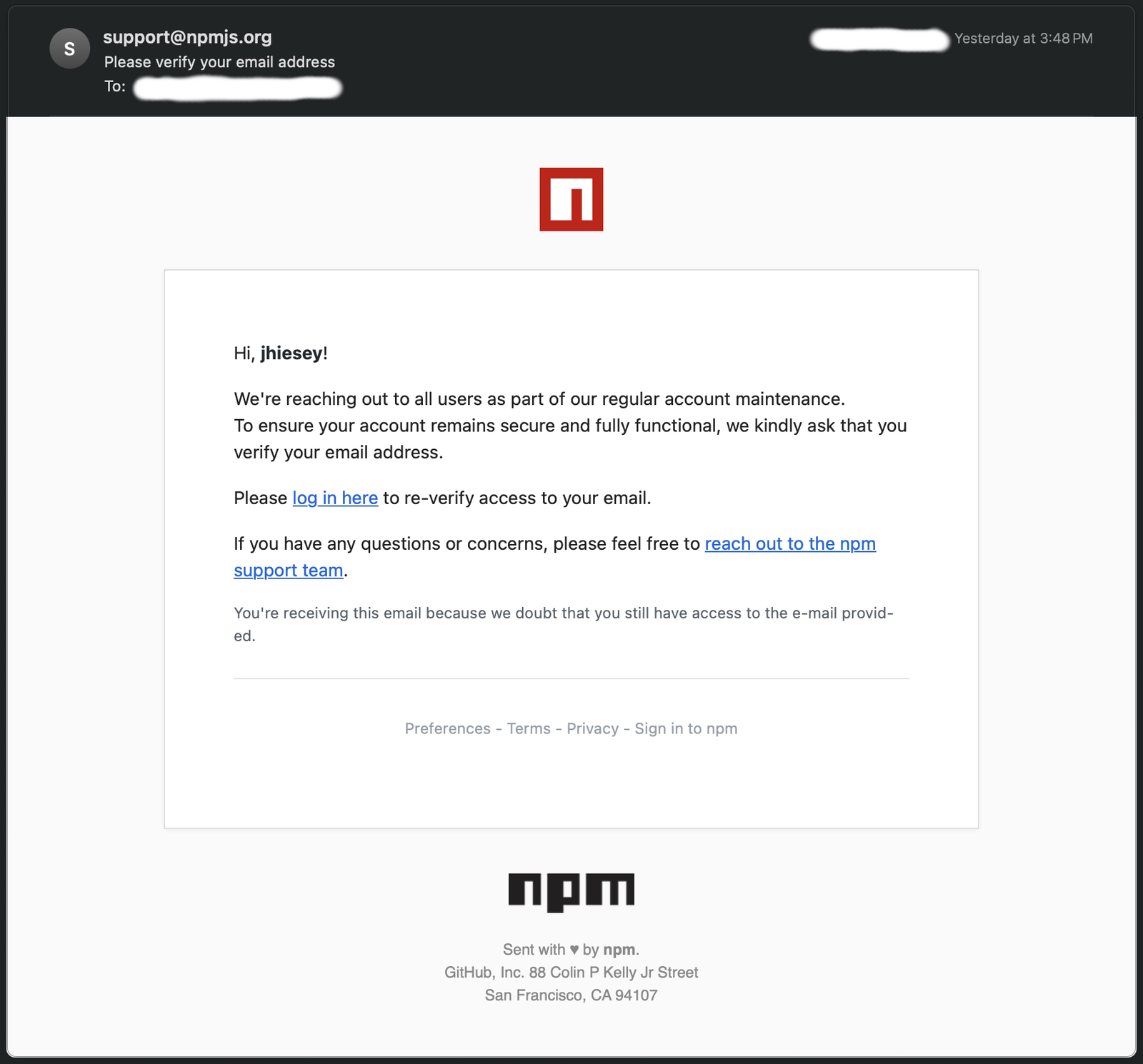
One of our engineers recently encountered a phishing email that attempted to impersonate npm, the Node.js package registry. The email spoofed the support@npmjs.org address and contained a link to npnjs.com (note the "n" instead of "m"). This domain is a full copy or proxy of the npm website, a sophisticated typosquatting attack aimed at stealing developer credentials.
The phishing email urged the recipient to “log in here” via a link like:https://npnjs.com/login?token=xxxxxx (token redacted).
Attackers often use tokens to track who clicked the link or to pre-fill victim data on the phishing site. It could also be used to generate a fake “session” to mimic npm’s login flow. The tokenized URL hints at semi-targeted efforts, potentially focusing on active package maintainers with significant reach. In this case, the targeted user is the maintainer of packages totaling 34 million weekly downloads.
Interestingly, the support links within the email pointed to the legitimate npmjs.com, adding credibility to the attack.
The email was flagged as spam and never reached the primary inbox. We have reported this incident to the npm security team.
The raw email headers and security scans revealed multiple red flags:
45.9.148.108 (hosted by Nice IT Customers Network). This IP has been reported 27 times on AbuseIPDB and is flagged by Criminal IP and VirusTotal.shosting-s0-n1.nicevps.net, a VPS host frequently used for malicious campaigns.npm accounts have become high-value targets for attackers. Compromising a single account can enable adversaries to publish malicious packages, potentially infecting millions of downstream projects.
Maintainers should be skeptical of verification requests. npm rarely asks for email verification unless you’ve initiated the action. Protect your account with two-factor authentication, and use scoped tokens instead of passwords for publishing packages.
The phishing email was caught by spam filters, but it shows how sophisticated and convincing some of these supply chain attacks are becoming. If there’s any suspicion of credential theft, rotate npm access tokens immediately. We reported the incident to npm to help prevent similar attacks against developers in the future.
Our analysis of the phishing email and infrastructure uncovered the following IOCs:
npnjs.com npmjs.com.https://npnjs.com/login?token=<redacted>support@npmjs.orgphl-compute-02.internal [10.202.2.42].SPF_NONE, RDNS_NONE, and VFY_ACCT_NORDNS).45.9.148.108 shosting-s0-n1.nicevps.net (Nice IT Customers Network).npmjs.com resources to enhance credibility.Subscribe to our newsletter
Get notified when we publish new security blog posts!
Try it now

Security News
This episode explores the hard problem of reachability analysis, from static analysis limits to handling dynamic languages and massive dependency trees.

Security News
/Research
Malicious Nx npm versions stole secrets and wallet info using AI CLI tools; Socket’s AI scanner detected the supply chain attack and flagged the malware.

Security News
CISA’s 2025 draft SBOM guidance adds new fields like hashes, licenses, and tool metadata to make software inventories more actionable.