Security News
curl Shuts Down Bug Bounty Program After Flood of AI Slop Reports
A surge of AI-generated vulnerability reports has pushed open source maintainers to rethink bug bounties and tighten security disclosure processes.
www.github.com/kleiton0x00/ppmap.git
Advanced tools
A simple scanner/exploitation tool written in GO which automatically exploits known and existing gadgets (checks for specific variables in the global context) to perform XSS via Prototype Pollution. NOTE: The program only exploits known gadgets, but does not cover code analysis or any advanced Prototype Pollution exploitation, which may include custom gadgets.
Make sure to have Chromium installed (Chrome will also do the job):
sudo apt-get install chromium-browser
Make sure to have chromedp installed:
go get -u github.com/chromedp/chromedp
The recommended way to install the software is to compile it yourself by executing:
go get -u github.com/kleiton0x00/ppmap.git
Check if it is successfuly compiled by typing in the terminal: ppmap
If you face error during manually compiling (for some reasons), you can download the precompiled one:
chmod +x ppmapUsing the program is very simple, you can either:
scan a directory/file (or even just the website itself):
echo 'https://target.com' | ppmap
or endpoint:
echo 'http://target.com/something/?page=home' | ppmap
For mass scanning:
cat url.txt | ppmap where url.txt contains all url(s) in column.
Feel free to test the tool on the following websites as a part of demonstration and to also check if the software is working correctly:
https://msrkp.github.io/pp/2.html
https://ctf.nikitastupin.com/pp/known.html
https://grey-acoustics.surge.sh
Many thanks to @Tomnomnom for the inspiration: https://www.youtube.com/watch?v=Gv1nK6Wj8qM&t=1558s
The workflow of this program is hugely based on this article: https://infosecwriteups.com/javascript-prototype-pollution-practice-of-finding-and-exploitation-f97284333b2
The fingerprint javascript file is based on this git: https://gist.github.com/nikitastupin/b3b64a9f8c0eb74ce37626860193eaec
FAQs
Unknown package
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Security News
A surge of AI-generated vulnerability reports has pushed open source maintainers to rethink bug bounties and tighten security disclosure processes.
Product
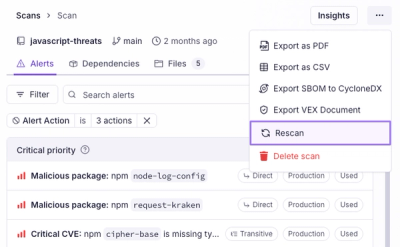
Scan results now load faster and remain consistent over time, with stable URLs and on-demand rescans for fresh security data.
Product
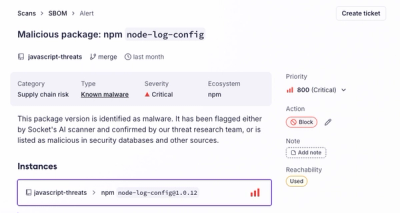
Socket's new Alert Details page is designed to surface more context, with a clearer layout, reachability dependency chains, and structured review.