
Security News
Feross on TBPN: Socket's Series C and the State of Software Supply Chain Security
Feross Aboukhadijeh joins TBPN to discuss Socket's $60M Series C, 500%+ ARR growth, AI's impact on open source, and the rise in supply chain attacks.
An OIDC authorization server building blocks with security and privacy by design philosophy.
This will not provide a full-featured standalone OIDC Server but a limited and secure settings according to your use cases :
online users using authorization_code flow with mandatory PKCE via Pushed
Authorization Request with state enforcement;machine-to-machine using client_credentials based on asymetric
authentication schemes;devices and constrained environments, you know for IO(v)T (Internet Of vulnerable Thing);offline users using refresh_token flow for application that need to
act as an online user but without its online interaction.impersonation / delegation using token_exchange flow fro resource server
who wants to access authenticated external resource on behalf of the subject
with a restricted resource level privilege set.I have been developing OAuth/OIDC/UMA providers since 2012, in multiple
languages and environments. People generally don't understand OIDC flows.
It's like driving a car that requires you to know how engine work and how the car is built. But the only thing you want is to drive your car.
OAuth / OIDC is often criticized in favor of SAML, but implementations are more vulnerables than the protocol itself. OAuth is just offered as a developer framework, but it's true to say that not all developers are aware of security problems.
Implementations are done by developers that don't have/take the time to browse the specification maze, they read them quickly with their own belief in mind. As a consequence the specifications are not understood but barely interpreted, that will produce faulty implementations.
Also security products are often associated with NIH syndrom.
What I observed in real life:
authorization_code because it doesn't have user/password in the
flow;client_credentials grant type to be used as customer credentials like
password grant type but for external customer user access (login form with
client credentials);client_credentials from a JS public UI (hardcoded client_secret);Many OIDC providers give you a lot of features that you have to understand and choose to maximize your security posture. So that your security posture is correlated to your understanding of OAuth and OIDC and their implementations in the product.
I don't like this idea to be honest.
I understand the requirements of commercial products to have a wide compatibility
matrix, but by allowing insecure settings for one client you can compromise the
the whole platform, and also lose the customer inside the feature fog.
But OAuth / OIDC specification are only tools in a toolbox, and they need to be orchestrated in a proper way to provide a simple, efficient and secure service.
That's the reason why I've started this project as an OSS project, to provide a simple and solid implementations of 4 OAuth flows.
solid can't pass the OIDC compliance tests;I made sample server and various integrations inside examples/ folder.
PAR+DPoP+JARM is enabled and enforced for authorization_code flow;hybrid flow is not and will be supported; Web applications must use server
side component (or lambda) to negociate authorizations; By design, your
client-side application code (JS) should not be exposed until you are identified;code will be supported to enforce server-side negociation;PKCE+Nonce is enforced by default for all client types during authorization_code
flow;authorization_code flow could not be started by the user-agent, as the
default behavior, the client must use PAR protocol to retrieve a request_uri
that will qualify and start the authorization_code flow;HSxxx / RSxxx support as JOSE signature algorithms;
HSxxx doesn't provide digital signature;RSxxx uses RSA algorithms that needs to have high computation to improve
security protection level so that it will be more difficult for constrained
environment (IoT) to have same security protection level as a normal application;elliptical curves involved algorithms will be used;access_token / refresh_token are hybrid tokens so that they embed protocol
validation details (expiration, etc.) without any privacy related info (sub).
These informations are referenced via an embeded jti claim that will address
an AS-only accessbile record that will contains extra data;audience parameter is mandatory for request that need scope in order to
target the corresponding application. This will allow various validations between
client and application, and consent management;PAR must use JWT encoded request payload to due request registration.private_key_jwt - https://oauth.net/private-key-jwt/attest_jwt_client_auth - OAuth 2.0 Attestation-Based Client Authenticationtls_client_auth - RFC8705 - OAuth 2.0 Mutual-TLS Client Authentication and Certificate-Bound Access Tokensclient_credentials grant typeauthorization_code grant type
refresh_token grant typeurn:ietf:params:oauth:grant-type:device_code grant type - rfc8628urn:ietf:params:oauth:grant-type:token-exchange grant type - rfc8693urn:openid:params:grant-type:cibagrant type - OpenID Connect Client Initiated Backchannel Authentication FlowFAQs
Unknown package
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Feross Aboukhadijeh joins TBPN to discuss Socket's $60M Series C, 500%+ ARR growth, AI's impact on open source, and the rise in supply chain attacks.

Security News
OSV withdrew 157 OSV malware reports after automated false positives incorrectly flagged trusted npm and PyPI packages, sending bad records into tools that rely on OSV data.
Research
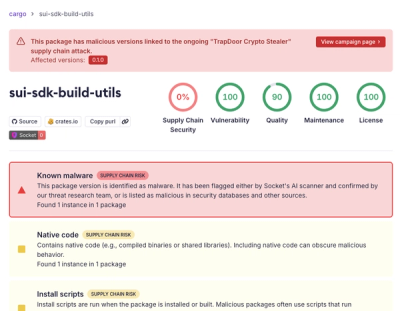
/Security News
TrapDoor crypto stealer hits 36 malicious packages across npm, PyPI, and Crates.io, targeting crypto, DeFi, AI, and security developers.