
Security News
Deno 2.6 + Socket: Supply Chain Defense In Your CLI
Deno 2.6 introduces deno audit with a new --socket flag that plugs directly into Socket to bring supply chain security checks into the Deno CLI.
com.github.monkeywie:proxyee
Advanced tools
HTTP proxy server,support HTTPS and websocket.MITM impl,intercept and tamper HTTPS traffic.
Proxyee is a JAVA written HTTP proxy server library that supports HTTP, HTTPS, Websocket protocols, and supports MITM (Man-in-the-middle), which can capture and tamper with HTTP, HTTPS packet.
<dependency>
<groupId>com.github.monkeywie</groupId>
<artifactId>proxyee</artifactId>
<version>1.7.6</version>
</dependency>
new HttpProxyServer().start(9999);
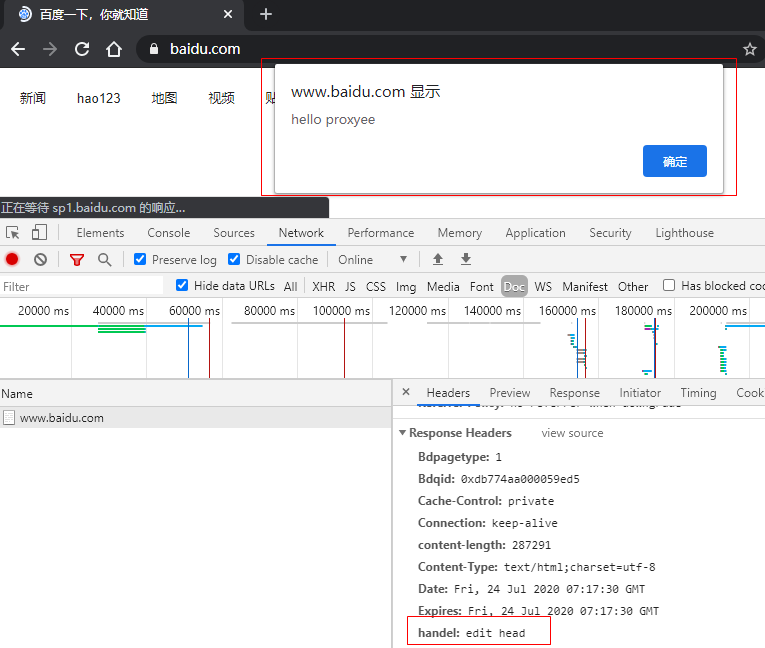
The following is a demonstration of a MITM attack that modifies the response header and response body when visiting the Baidu homepage, as shown in the figure below:
Code:
HttpProxyServerConfig config = new HttpProxyServerConfig();
//enable HTTPS support
//If not enabled, HTTPS will not be intercepted, but forwarded directly to the raw packet.
config.setHandleSsl(true);
new HttpProxyServer()
.serverConfig(config)
.proxyInterceptInitializer(new HttpProxyInterceptInitializer() {
@Override
public void init(HttpProxyInterceptPipeline pipeline) {
pipeline.addLast(new FullResponseIntercept() {
@Override
public boolean match(HttpRequest httpRequest, HttpResponse httpResponse, HttpProxyInterceptPipeline pipeline) {
//Insert js when matching to Baidu homepage
return HttpUtil.checkUrl(pipeline.getHttpRequest(), "^www.baidu.com$")
&& isHtml(httpRequest, httpResponse);
}
@Override
public void handleResponse(HttpRequest httpRequest, FullHttpResponse httpResponse, HttpProxyInterceptPipeline pipeline) {
//Print raw packet
System.out.println(httpResponse.toString());
System.out.println(httpResponse.content().toString(Charset.defaultCharset()));
//Edit response header and response body
httpResponse.headers().set("handel", "edit head");
httpResponse.content().writeBytes("<script>alert('hello proxyee')</script>".getBytes());
}
});
}
})
.start(9999);
Note: When https support is enabled, you need to install the CA certificate (
src/resources/ca.crt) to a trusted root certificate authority.
More demo code can be found in the test package.
The CA certificate (src/resources/ca.crt) from the project needs to be imported to a trusted root certificate authority. You can use the CertDownIntercept interceptor to enable the web certificate download feature, visit http://serverIP:serverPort to access.
Note 1: If the certificate installation on Android phones pops up the password stored in your credentials, just enter the lock screen password.
Note 2: Android 7 and above, the system no longer trusts user-installed certificates, you need to root and use the cat ca.crt > $(openssl x509 -inform PEM -subject_hash_old -in ca.crt | head -1).0 command generates the d1488b25.0 file, and then moves the file to the /system/etc/security/cacerts/ And give 644 access.
Note 3: In Android 7 and above, even if you add the certificate to the system certificate, this certificate does not work in chrome. The reason is that chrome will only trust certificates with validity less than 27 months from 2018 (https://www.entrustdatacard.com/blog/2018/february/chrome-requires-ct-after-april-2018). So you need to generate the certificate file yourself.
Since the root certificate and private key attached to the project are public, they are only suitable for local development and debugging, please generate your own root certificate and private key when using in the official environment, otherwise there will be risks.
running the main method of thecom.github.monkeywie.proxyee.crt.CertUtil class
use openssl
If you only want to perform MITM attacks on certain domains, you can use the HttpProxyServerConfig.setMitmMatcher method to set the matching rule, for example:
HttpProxyServerConfig config = new HttpProxyServerConfig();
config.setHandleSsl(true);
// only MITM on www.baidu.com
config.setMitmMatcher(new DomainHttpProxyMitmMatcher(Arrays.asList("www.baidu.com")));
Now the built-in DomainHttpProxyMitmMatcher is an exact match for the request domain. If you have other requirements, you can implement the HttpProxyMitmMatcher interface to customize the matching rules.
openssl genrsa -out ca.key 2048
openssl pkcs8 -topk8 -nocrypt -inform PEM -outform DER -in ca.key -out ca_private.der
openssl req -sha256 -new -x509 -days 365 -key ca.key -out ca.crt \
-subj "/C=CN/ST=GD/L=SZ/O=lee/OU=study/CN=testRoot"
Copy ca.crt and ca_private.der to the project src/resources/ after generation, or implement the HttpProxyCACertFactory interface to custom load the root certificate and private key.
Currently only basic authentication are supported.
// curl -i -x 127.0.0.1:9999 -U admin:123456 http://www.baidu.com
HttpProxyServerConfig config = new HttpProxyServerConfig();
config.setAuthenticationProvider(new BasicHttpProxyAuthenticationProvider() {
@Override
protected BasicHttpToken authenticate(String usr, String pwd) {
if ("admin".equals(usr) && "123456".equals(pwd)) {
return new BasicHttpToken(usr, pwd);
}
return null;
}
});
new HttpProxyServer()
.serverConfig(config)
.start(9999);
Customize authentication by implementing the HttpProxyAuthenticationProvider interface.
After the authorization, the token returned from the verification pass can be obtained in the pipeline.
HttpToken token = HttpAuthContext.getToken(clientChannel);
Pre-proxy can be set,support http,socks4,socks5 protocol.
new HttpProxyServer()
.proxyConfig(new ProxyConfig(ProxyType.SOCKS5, "127.0.0.1", 1085))
.start(9999);
If you like this project, please consider donating to support the development of this project, thank you!
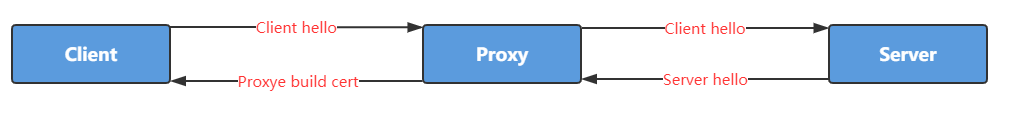
SSL handshake
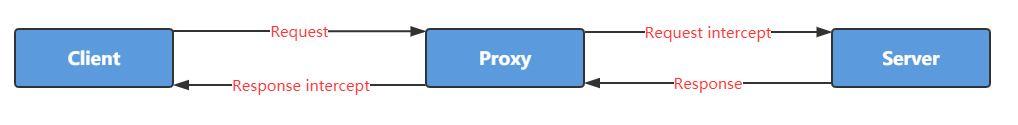
HTTP communication
FAQs
HTTP proxy server,support HTTPS and websocket.MITM impl,intercept and tamper HTTPS traffic.
We found that com.github.monkeywie:proxyee demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 0 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Deno 2.6 introduces deno audit with a new --socket flag that plugs directly into Socket to bring supply chain security checks into the Deno CLI.

Security News
New DoS and source code exposure bugs in React Server Components and Next.js: what’s affected and how to update safely.
Security News
Socket CEO Feross Aboukhadijeh joins Software Engineering Daily to discuss modern software supply chain attacks and rising AI-driven security risks.