
Security News
Nx npm Packages Compromised in Supply Chain Attack Weaponizing AI CLI Tools
Malicious Nx npm versions stole secrets and wallet info using AI CLI tools; Socket’s AI scanner detected the supply chain attack and flagged the malware.
@abernier/create-sandbox
Advanced tools
[](https://www.npmjs.com/package/@abernier/create-sandbox)
It's codesandox but as a local command-line!
Command to create a standard CRA, but:
src/App.js[3000..4000] to launch the localhost hot-reload serverThe following command will create a new random-name-2345 project into .
$ npm init @abernier/sandbox
or
$ yarn create @abernier/sandbox
$ npm init @abernier/sandbox ~/tmp
A random-name-2345 will be created inside ~/tmp and your CRA created into.
$ npm init @abernier/sandbox ~/code/rosie
A rosie folder will be created and your CRA created into.
NB: no random name here as you specify a non-existing folder name
npxAlternatively to you could just:
$ npx @abernier/create-sandbox
but this is less cool
Ready to publish a new version to NPM registry?
package.json versionnpm login if not alreadynpm publishIf successful, you should want to tag the version:
$ git add package.json
$ git commit -m "bump version"
$ git tag v1.0.1
$ git push --tags
Pre-requisite:
NPM_TOKEN secret (in Settings > Secrets and as referenced into ci.yml file)Then, to release a new version on npm:
package.json version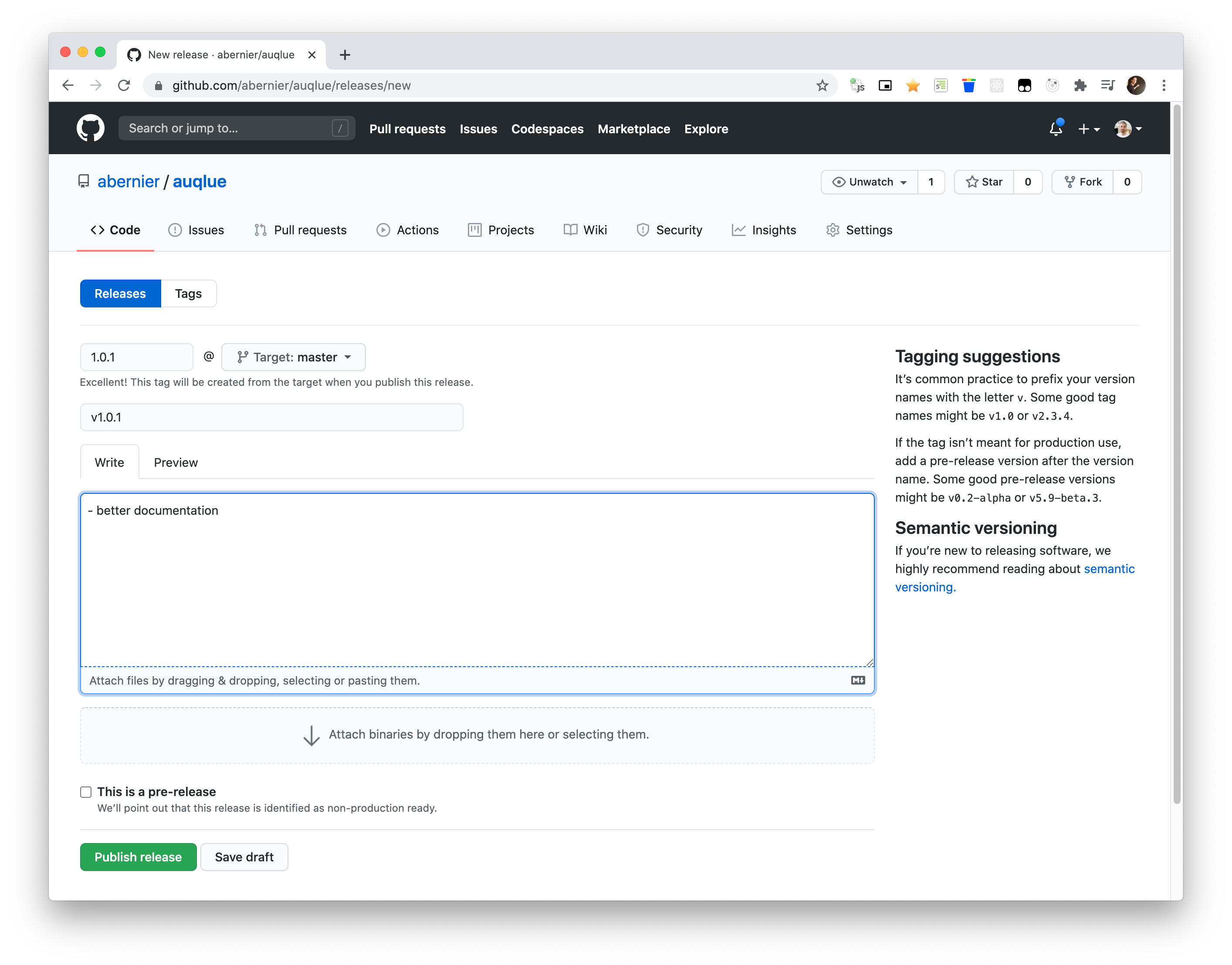
FAQs
[](https://www.npmjs.com/package/@abernier/create-sandbox)
We found that @abernier/create-sandbox demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Malicious Nx npm versions stole secrets and wallet info using AI CLI tools; Socket’s AI scanner detected the supply chain attack and flagged the malware.

Security News
CISA’s 2025 draft SBOM guidance adds new fields like hashes, licenses, and tool metadata to make software inventories more actionable.

Security News
A clarification on our recent research investigating 60 malicious Ruby gems.