
Security News
MCP Steering Committee Launches Official MCP Registry in Preview
The MCP Steering Committee has launched the official MCP Registry in preview, a central hub for discovering and publishing MCP servers.
@algoan/connect
Advanced tools
Library for Algoan Connect
<script type="text/javascript" src="https://js.algoan.com/connect/algoan-connect.js"></script>
npm install @algoan/connect
Place a div with the id algoan-connect where you want the button to appear:
<div id="algoan-connect"></div>
Then, you can invoke the Algoan Connect library:
<script>
AlgoanConnect.addWidget({ apiKey: '<Your API key>', customIdentifier: '<Your unique user identifier>' });
</script>
import { addWidget } from '@algoan/connect';
addWidget({ apiKey: '<Your API key>', customIdentifier: '<Your unique user identifier>' });
It is possible to configure some aspect of the Algoan Connect button. You can refer to the connect customization file for the list of every configuration possible.
Once the widget is added to your user interface, it is possible to pass extra information to each aggregation request. For this use case, you can use setCustomerPersonalDetails.
npm install
npm run build
npm run compile
npm run dev
This command will start a webserver listening at http://localhost:3002/. It will serve the dev/dev-server-template.html file with the library already injected.
FAQs
Library for Algoan Connect
We found that @algoan/connect demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 3 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
The MCP Steering Committee has launched the official MCP Registry in preview, a central hub for discovering and publishing MCP servers.

Product
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
Research
/Security News
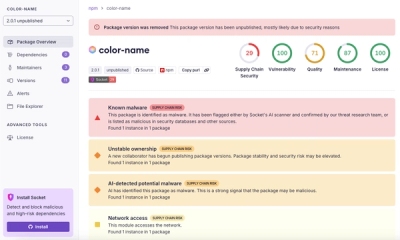
npm author Qix’s account was compromised, with malicious versions of popular packages like chalk-template, color-convert, and strip-ansi published.