Product
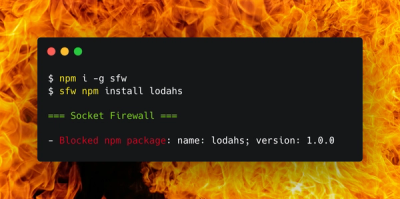
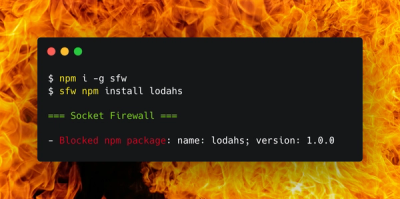
Introducing Socket Firewall: Free, Proactive Protection for Your Software Supply Chain
Socket Firewall is a free tool that blocks malicious packages at install time, giving developers proactive protection against rising supply chain attacks.
@digix/eth-lightwallet
Advanced tools
A minimal ethereum javascript wallet.
LightWallet is a HD wallet that can store your private keys encrypted in the browser to allow you to run Ethereum dapps even if you're not running a local Ethereum node. It uses BIP32 and BIP39 to generate an HD tree of addresses from a randomly generated 12-word seed.
LightWallet is primarily intended to be a signing provider for the Hooked Web3 provider through the keystore module. This allows you to have full control over your private keys while still connecting to a remote node to relay signed transactions. Moreover, the txutils functions can be used to construct transactions when offline, for use in e.g. air-gapped coldwallet implementations.
The default BIP32 HD derivation path has been m/0'/0'/0'/i, but any HD path can be chosen.
Please note that LightWallet has not been through a comprehensive security review at this point. It is still experimental software, intended for small amounts of Ether to be used for interacting with smart contracts on the Ethereum blockchain. Do not rely on it to store larger amounts of Ether yet.
npm install eth-lightwallet
The eth-lightwallet package contains dist/lightwallet.min.js that can be included in an HTML page:
<html>
<body>
<script src="lightwallet.min.js"></script>
</body>
</html>
The file lightwallet.min.js exposes the global object lightwallet to the browser which has the two main modules lightwallet.keystore and lightwallet.txutils.
Sample recommended usage with hooked web3 provider:
// the seed is stored encrypted by a user-defined password
var password = prompt('Enter password for encryption', 'password');
keyStore.createVault({
password: password,
// seedPhrase: seedPhrase, // Optionally provide a 12-word seed phrase
// salt: fixture.salt, // Optionally provide a salt.
// A unique salt will be generated otherwise.
// hdPathString: hdPath // Optional custom HD Path String
}, function (err, ks) {
// Some methods will require providing the `pwDerivedKey`,
// Allowing you to only decrypt private keys on an as-needed basis.
// You can generate that value with this convenient method:
ks.keyFromPassword(password, function (err, pwDerivedKey) {
if (err) throw err;
// generate five new address/private key pairs
// the corresponding private keys are also encrypted
ks.generateNewAddress(pwDerivedKey, 5);
var addr = ks.getAddresses();
ks.passwordProvider = function (callback) {
var pw = prompt("Please enter password", "Password");
callback(null, pw);
};
// Now set ks as transaction_signer in the hooked web3 provider
// and you can start using web3 using the keys/addresses in ks!
});
});
Sample old-style usage with hooked web3 provider (still works, but less secure because uses fixed salts).
// generate a new BIP32 12-word seed
var secretSeed = lightwallet.keystore.generateRandomSeed();
// the seed is stored encrypted by a user-defined password
var password = prompt('Enter password for encryption', 'password');
lightwallet.keystore.deriveKeyFromPassword(password, function (err, pwDerivedKey) {
var ks = new lightwallet.keystore(secretSeed, pwDerivedKey);
// generate five new address/private key pairs
// the corresponding private keys are also encrypted
ks.generateNewAddress(pwDerivedKey, 5);
var addr = ks.getAddresses();
// Create a custom passwordProvider to prompt the user to enter their
// password whenever the hooked web3 provider issues a sendTransaction
// call.
ks.passwordProvider = function (callback) {
var pw = prompt("Please enter password", "Password");
callback(null, pw);
};
// Now set ks as transaction_signer in the hooked web3 provider
// and you can start using web3 using the keys/addresses in ks!
});
keystore Function definitionsThese are the interface functions for the keystore object. The keystore object holds a 12-word seed according to BIP39 spec. From this seed you can generate addresses and private keys, and use the private keys to sign transactions.
Note: Addresses and RLP encoded data are in the form of hex-strings. Hex-strings start with 0x.
keystore.createVault(options, callback)This is the interface to create a new lightwallet keystore.
BIP39 compliant HD Path String. Previously the default has been m/0'/0'/0', another popular one is the BIP44 path string m/44'/60'/0'/0.keystore.keyFromPassword(password, callback)This instance method uses any internally-configured salt to return the appropriate pwDerivedKey.
Takes the user's password as input and generates a symmetric key of type Uint8Array that is used to encrypt/decrypt the keystore.
keystore.isDerivedKeyCorrect(pwDerivedKey)Returns true if the derived key can decrypt the seed, and returns false otherwise.
keystore.generateRandomSeed([extraEntropy])Generates a string consisting of a random 12-word seed and returns it. If the optional argument string extraEntropy is present the random data from the Javascript RNG will be concatenated with extraEntropy and then hashed to produce the final seed. The string extraEntropy can be something like entropy from mouse movements or keyboard presses, or a string representing dice throws.
keystore.isSeedValid(seed)Checks if seed is a valid 12-word seed according to the BIP39 specification.
keystore.generateNewAddress(pwDerivedKey, [num])Allows the vault to generate additional internal address/private key pairs.
The simplest usage is ks.generateNewAddress(pwDerivedKey).
Generates num new address/private key pairs (defaults to 1) in the keystore from the seed phrase, which will be returned with calls to ks.getAddresses().
keystore.deserialize(serialized_keystore)Takes a serialized keystore string serialized_keystore and returns a new keystore object.
keystore.serialize()Serializes the current keystore object into a JSON-encoded string and returns that string.
keystore.getAddresses()Returns a list of hex-string addresses currently stored in the keystore.
keystore.getSeed(pwDerivedKey)Given the pwDerivedKey, decrypts and returns the users 12-word seed.
keystore.exportPrivateKey(address, pwDerivedKey)Given the derived key, decrypts and returns the private key corresponding to address. This should be done sparingly as the recommended practice is for the keystore to sign transactions using signing.signTx, so there is normally no need to export private keys.
upgrade Function definitionskeystore.upgradeOldSerialized(oldSerialized, password, callback)Takes a serialized keystore in an old format and a password. The callback takes the upgraded serialized keystore as its second argument.
signing Function definitionssigning.signTx(keystore, pwDerivedKey, rawTx, signingAddress, hdPathString)Signs a transaction with the private key corresponding to signingAddress.
keystore: An instance of the keystore with which to sign the TX with.pwDerivedKey: the users password derived key (Uint8Array)rawTx: Hex-string defining an RLP-encoded raw transaction.signingAddress: hex-string defining the address to send the transaction from.hdPathString: (Optional) A path at which to create the encryption keys.Hex-string corresponding to the RLP-encoded raw transaction.
signing.signMsg(keystore, pwDerivedKey, rawMsg, signingAddress, hdPathString)Creates and signs a sha3 hash of a message with the private key corresponding to signingAddress.
keystore: An instance of the keystore with which to sign the TX with.pwDerivedKey: the users password derived key (Uint8Array)rawMsg: Message to be signedsigningAddress: hex-string defining the address corresponding to the signing private key.hdPathString: (Optional) A path at which to create the encryption keys.Signed hash as signature object with v, r and s values.
signing.signMsgHash(keystore, pwDerivedKey, msgHash, signingAddress, hdPathString)Signs a sha3 message hash with the private key corresponding to signingAddress.
keystore: An instance of the keystore with which to sign the TX with.pwDerivedKey: the users password derived key (Uint8Array)msgHash: SHA3 hash to be signedsigningAddress: hex-string defining the address corresponding to the signing private key.hdPathString: (Optional) A path at which to create the encryption keys.Signed hash as signature object with v, r and s values.
signing.concatSig(signature)Concatenates signature object to return signature as hex-string in the same format as eth_sign does.
signature: Signature object as returned from signMsg or ``signMsgHash`.Concatenated signature object as hex-string.
signing.recoverAddress(rawMsg, v, r, s)Recovers the signing address from the message rawMsg and the signature v, r, s.
encryption Function definitionsencryption.multiEncryptString(keystore, pwDerivedKey, msg, myAddress, theirPubKeyArray)NOTE: The format of encrypted messages has not been finalized and may change at any time, so only use this for ephemeral messages that do not need to be stored encrypted for a long time.
Encrypts the string msg with a randomly generated symmetric key, then encrypts that symmetric key assymetrically to each of the pubkeys in theirPubKeyArray. The encrypted message can then be read only by sender and the holders of the private keys corresponding to the public keys in theirPubKeyArray. The returned object has the following form, where nonces and ciphertexts are encoded in base64:
{ version: 1,
asymAlg: 'curve25519-xsalsa20-poly1305',
symAlg: 'xsalsa20-poly1305',
symNonce: 'SLmxcH3/CPMCCJ7orkI7iSjetRlMmzQH',
symEncMessage: 'iN4+/b5InlsVo5Bc7GTmaBh8SgWV8OBMHKHMVf7aq5O9eqwnIzVXeX4yzUWbw2w=',
encryptedSymKey:
[ { nonce: 'qcNCtKqiooYLlRuIrNlNVtF8zftoT5Cb',
ciphertext: 'L8c12EJsFYM1K7udgHDRrdHhQ7ng+VMkzOdVFTjWu0jmUzpehFeqyoEyg8cROBmm' },
{ nonce: 'puD2x3wmQKu3OIyxgJq2kG2Hz01+dxXs',
ciphertext: 'gLYtYpJbeFKXL/WAK0hyyGEelaL5Ddq9BU3249+hdZZ7xgTAZVL8tw+fIVcvpgaZ' },
{ nonce: '1g8VbftPnjc+1NG3zCGwZS8KO73yjucu',
ciphertext: 'pftERJOPDV2dfP+C2vOwPWT43Q89V74Nfu1arNQeTMphSHqVuUXItbyCMizISTxG' },
{ nonce: 'KAH+cCxbFGSDjHDOBzDhMboQdFWepvBw',
ciphertext: 'XWmmBmxLEyLTUmUBiWy2wDqedubsa0KTcufhKM7YfJn/eHWhDDptMxYDvaKisFmn' } ] }
Note that no padding is applied to msg, so it's possible to deduce the length of the string msg from the ciphertext. If you don't want this information to be known, please apply padding to msg before calling this function.
encryption.multiDecryptString(keystore, pwDerivedKey, encMsg, theirPubKey, myAddress)Decrypt a message encMsg created with the function
multiEncryptString(). If successful, returns the original message
string. If not successful, returns false.
encryption.addressToPublicEncKey(keystore, pwDerivedKey, address)Gets the public encryption key corresponding to the private key of address in the keystore.
txutils Function definitionsThese are the interface functions for the txutils module. These functions will create RLP encoded raw unsigned transactions which can be signed using the keystore.signTx() command.
txutils.createContractTx(fromAddress, txObject)Using the data in txObject, creates an RLP-encoded transaction that will create the contract with compiled bytecode defined by txObject.data. Also computes the address of the created contract.
fromAddress: Address to send the transaction fromtxObject.gasLimit: Gas limittxObject.gasPrice: Gas pricetxObject.value: Endowment (optional)txObject.nonce: Nonce of fromAddresstxObject.data: Compiled code of the contractObject obj with fields
obj.tx: RLP encoded transaction (hex string)obj.addr: Address of the created contracttxutils.functionTx(abi, functionName, args, txObject)Creates a transaction calling a function with name functionName, with arguments args conforming to abi. The function is defined in a contract with address txObject.to.
abi: Json-formatted ABI as returned from the solc compilerfunctionName: string with the function nameargs: Array with the arguments to the functiontxObject.to: Address of the contracttxObject.gasLimit: Gas limittxObject.gasPrice: Gas pricetxObject.value: Value to sendtxObject.nonce: Nonce of sending addressRLP-encoded hex string defining the transaction.
txutils.valueTx(txObject)Creates a transaction sending value to txObject.to.
txObject.to: Address to send totxObject.gasLimit: Gas limittxObject.gasPrice: Gas pricetxObject.value: Value to sendtxObject.nonce: Nonce of sending addressRLP-encoded hex string defining the transaction.
See the file example_usage.js for usage of keystore and txutils in node.
See the file example_web.html for an example of how to use the LightWallet keystore together with the Hooked Web3 Provider in the browser.
Run all tests:
npm run test
npm run coverage
MIT License.
FAQs
A lightweight ethereum javascript wallet.
We found that @digix/eth-lightwallet demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 8 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Product
Socket Firewall is a free tool that blocks malicious packages at install time, giving developers proactive protection against rising supply chain attacks.

Research
Socket uncovers malicious Rust crates impersonating fast_log to steal Solana and Ethereum wallet keys from source code.

Research
A malicious package uses a QR code as steganography in an innovative technique.