
Security News
New CNAPulse Dashboard Tracks CNA Activity and Disclosure Trends
Open source dashboard CNAPulse tracks CVE Numbering Authorities’ publishing activity, highlighting trends and transparency across the CVE ecosystem.
@phormal/use-email
Advanced tools
Phormal is a library for generating forms, giving them beautiful styles and validating the data in them. We want to help developers stay focused on their business logic while building forms, instead of spending countless hours on perfecting things such as
Phormal is a library for generating forms, giving them beautiful styles and validating the data in them. We want to help developers stay focused on their business logic while building forms, instead of spending countless hours on perfecting things such as checkbox styles, or on validating zip codes for different countries. The goal is to provide a "works out of the box" experience, for 90% of the use cases, and to allow for customization when needed.
The documentation site is currently under construction, and will be available at: https://phormal.dev/
FAQs
Phormal is a library for generating forms, giving them beautiful styles and validating the data in them. We want to help developers stay focused on their business logic while building forms, instead of spending countless hours on perfecting things such as
We found that @phormal/use-email demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Open source dashboard CNAPulse tracks CVE Numbering Authorities’ publishing activity, highlighting trends and transparency across the CVE ecosystem.
Product
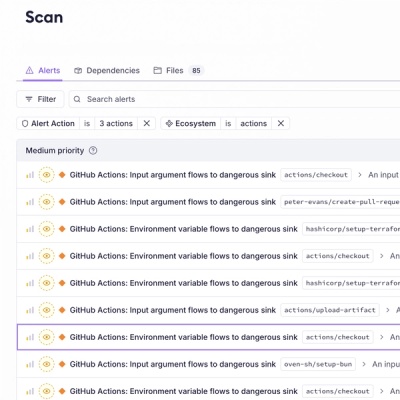
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.
Product
Add real-time Socket webhook events to your workflows to automatically receive pull request scan results and security alerts in real time.