
Research
Supply Chain Attack on Axios Pulls Malicious Dependency from npm
A supply chain attack on Axios introduced a malicious dependency, plain-crypto-js@4.2.1, published minutes earlier and absent from the project’s GitHub releases.
@sematext/logagent
Advanced tools
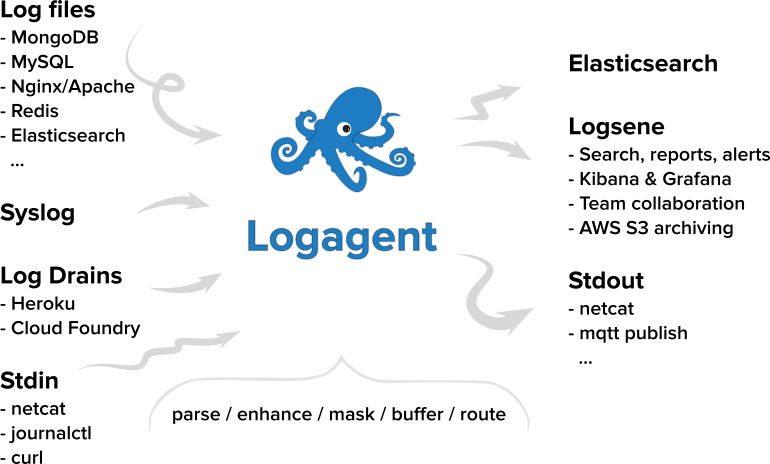
Logagent is a modern, open-source, light-weight log shipper. It is like Filebeat and Logstash in one, without the JVM memory footprint. It comes with out of the box and extensible log parsing, on-disk buffering, secure transport, and bulk indexing to Elasticsearch, Sematext Logs, and other destinations. Its low memory footprint and low CPU overhead make it suitable for deploying on edge nodes and devices, while its ability to parse and structure logs makes it a great Logstash alternative.
Details about the the Logagent Docker image are described in the Docker Hub Readme
1) Install Node.js
Official Node.js downloads and instructions. E.g. for Debian/Ubuntu:
curl -sL https://deb.nodesource.com/setup_10.x | sudo -E bash -
sudo apt-get install -y nodejs
Install Logagent with npm
sudo npm i -g @sematext/logagent
2) Run logagent command line tool
logagent --help
3) Example: Index your log files in Elasticsearch
logagent -e http://localhost:9200 -i logs -g ‘/var/log/**/*.log’
4) Optional: Install service & config
Install service for Logagent using systemd, upstart, launchd To quickly create a config file for indexing into Elasticsearch without having to edit it run something like this:
sudo logagent-setup -u http://localhost:9200 -i INDEX_NAME -g '/var/log/**/*.log'
# Logsene US: use -u https://logsene-receiver.sematext.com and your Logsene App Token as index name.
# Logsene EU: use -u https://logsene-receiver.eu.sematext.com and your Logsene App Token as index name.
Configuration
To configure different inputs, different event processing, or different outputs (e.g. your own Elasticsearch) edit /etc/sematext/logagent.conf, e.g.:
output:
logsene:
module: elasticsearch
url: http://elasticsearch-server:9200
index: logs
Then restart the service with sudo service logagent restart. Troubleshooting & Logs Logagent’s own logs:
/var/log/upstart/logagent.logjournalctl -u logagent/Library/Logs/logagent.logLocation of service scripts:
/etc/init/logagent.conf/etc/systemd/system/logagent.service/Library/LaunchDaemons/com.sematext.logagent.plistStart/stop service:
service logagent stop/startsystemctl stop/start logagentlaunchctl start/stop com.sematext.logagentFAQs
Smart log parser written in Node
The npm package @sematext/logagent receives a total of 33 weekly downloads. As such, @sematext/logagent popularity was classified as not popular.
We found that @sematext/logagent demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 2 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Research
A supply chain attack on Axios introduced a malicious dependency, plain-crypto-js@4.2.1, published minutes earlier and absent from the project’s GitHub releases.

Research
Malicious versions of the Telnyx Python SDK on PyPI delivered credential-stealing malware via a multi-stage supply chain attack.

Security News
TeamPCP is partnering with ransomware group Vect to turn open source supply chain attacks on tools like Trivy and LiteLLM into large-scale ransomware operations.