@snytch/nextjs
Advanced tools
@snytch/nextjs - npm Package Compare versions
+1
-1
| { | ||
| "name": "@snytch/nextjs", | ||
| "version": "0.1.3", | ||
| "version": "0.1.4", | ||
| "description": "Bundle scanning, NEXT_PUBLIC_ exposure detection, and environment drift for Next.js", | ||
@@ -5,0 +5,0 @@ "type": "module", |
+36
-32
@@ -57,3 +57,3 @@ # @snytch/nextjs | ||
|  | ||
|  | ||
@@ -75,8 +75,8 @@ ### `snytch check` | ||
| | Option | Default | Description | | ||
| | ----------- | ------------- | ------------------------------------------------------- | | ||
| | `--env` | auto-detected | Path to a `.env` file. Repeat for multiple files. | | ||
| | `--json` | off | Output results as JSON | | ||
| | Option | Default | Description | | ||
| | ----------- | ------------- | ---------------------------------------------------------------------- | | ||
| | `--env` | auto-detected | Path to a `.env` file. Repeat for multiple files. | | ||
| | `--json` | off | Output results as JSON | | ||
| | `--report` | off | Generate an HTML report at `./snytch-reports/snytch-check-report.html` | | ||
| | `--fail-on` | `critical` | Exit code threshold: `critical`, `warning`, or `all` | | ||
| | `--fail-on` | `critical` | Exit code threshold: `critical`, `warning`, or `all` | | ||
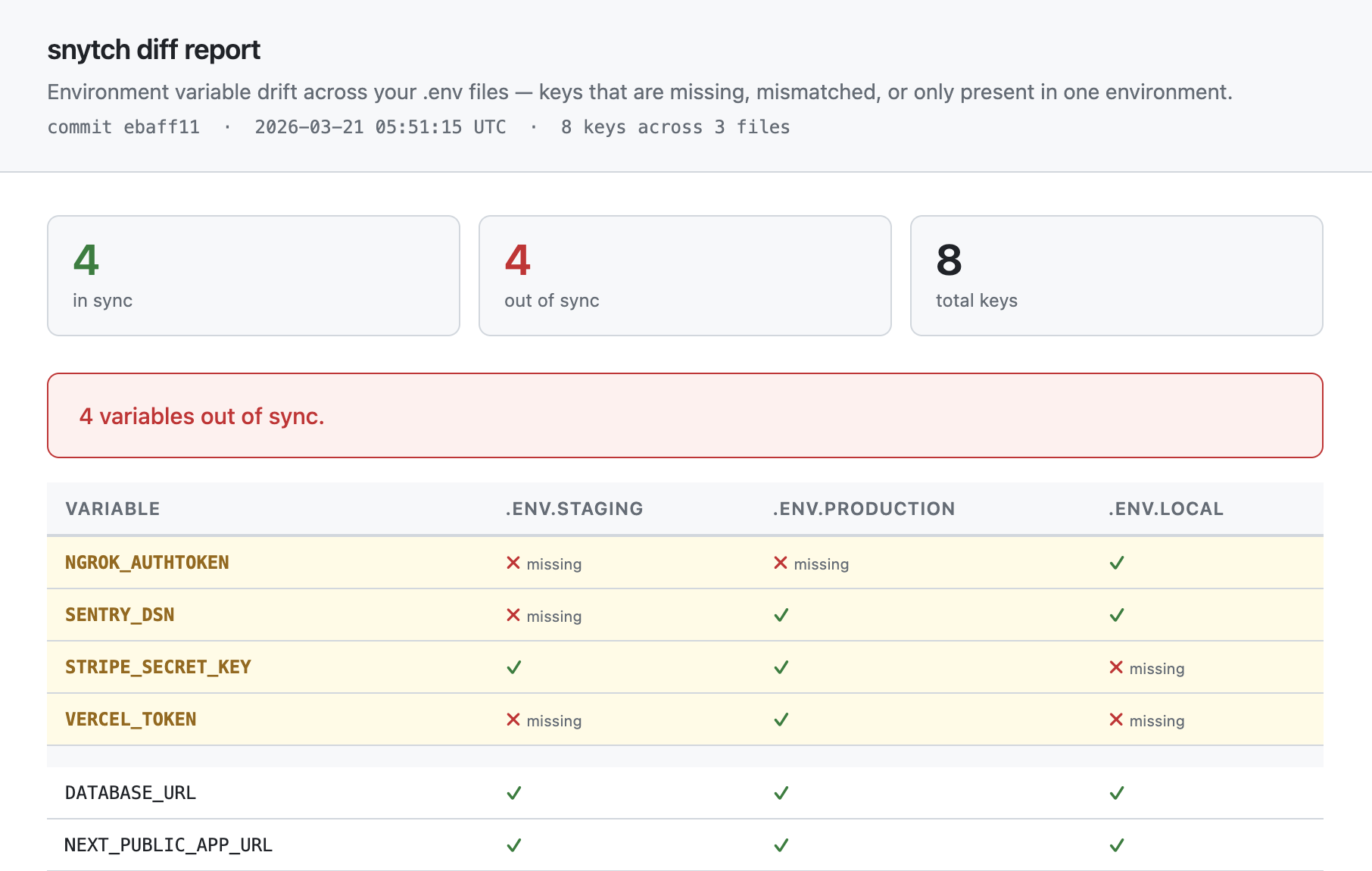
@@ -100,10 +100,10 @@ ### `snytch diff` | ||
| | Option | Default | Description | | ||
| | ---------- | -------- | ------------------------------------------------------- | | ||
| | `--env` | required | Path to a `.env` file. Must be provided at least twice. | | ||
| | `--json` | off | Output results as JSON | | ||
| | `--report` | off | Generate an HTML report at `./snytch-reports/snytch-diff-report.html` | | ||
| | `--strict` | off | Exit 1 for any drift, not just `serverOnly` keys | | ||
| | Option | Default | Description | | ||
| | ---------- | -------- | --------------------------------------------------------------------- | | ||
| | `--env` | required | Path to a `.env` file. Must be provided at least twice. | | ||
| | `--json` | off | Output results as JSON | | ||
| | `--report` | off | Generate an HTML report at `./snytch-reports/snytch-diff-report.html` | | ||
| | `--strict` | off | Exit 1 for any drift, not just `serverOnly` keys | | ||
|  | ||
|  | ||
@@ -130,7 +130,7 @@ ### `snytch mcp` | ||
| | File | Contents | | ||
| | ------------------------------------------- | -------------------------------------------------- | | ||
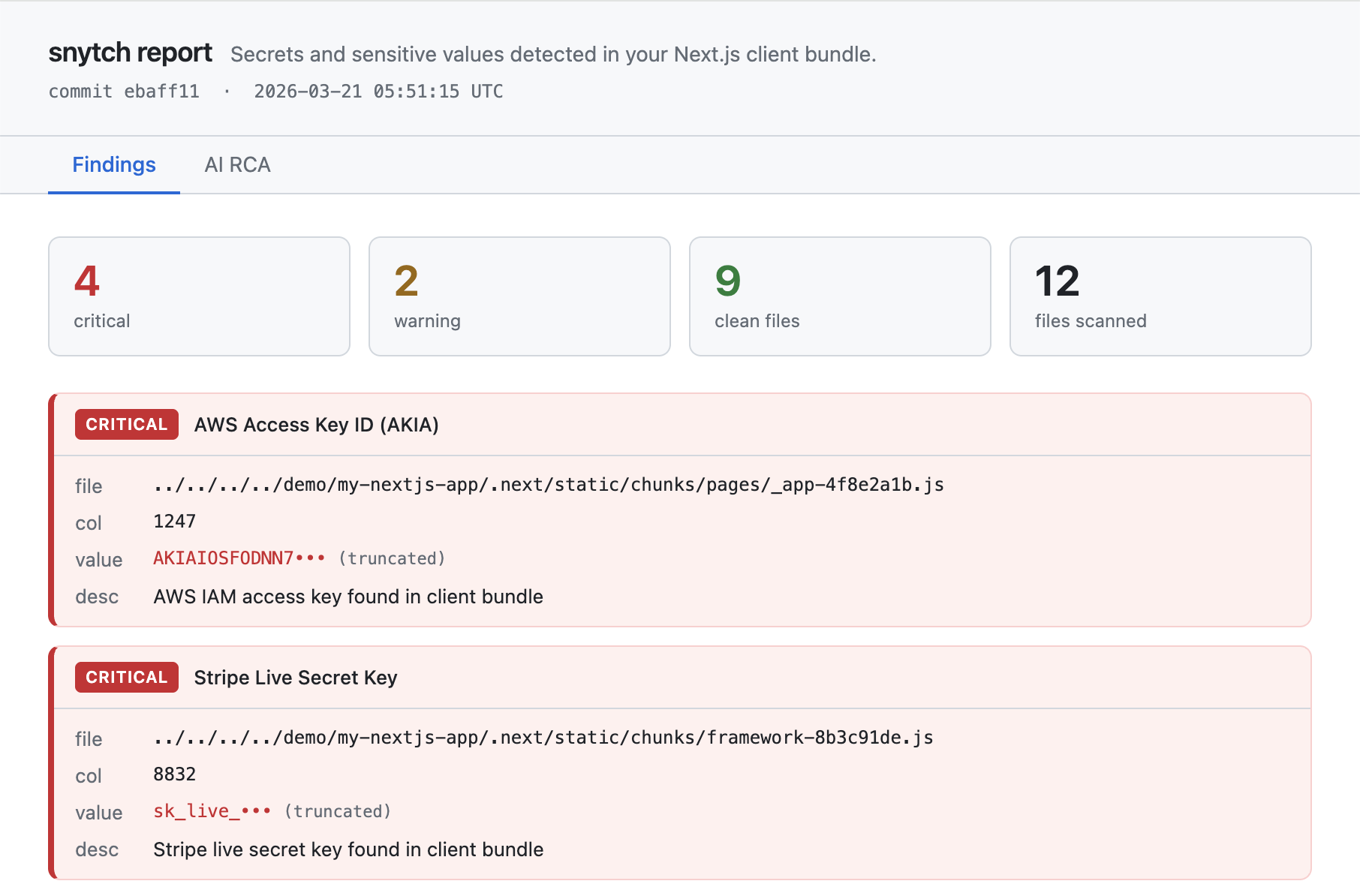
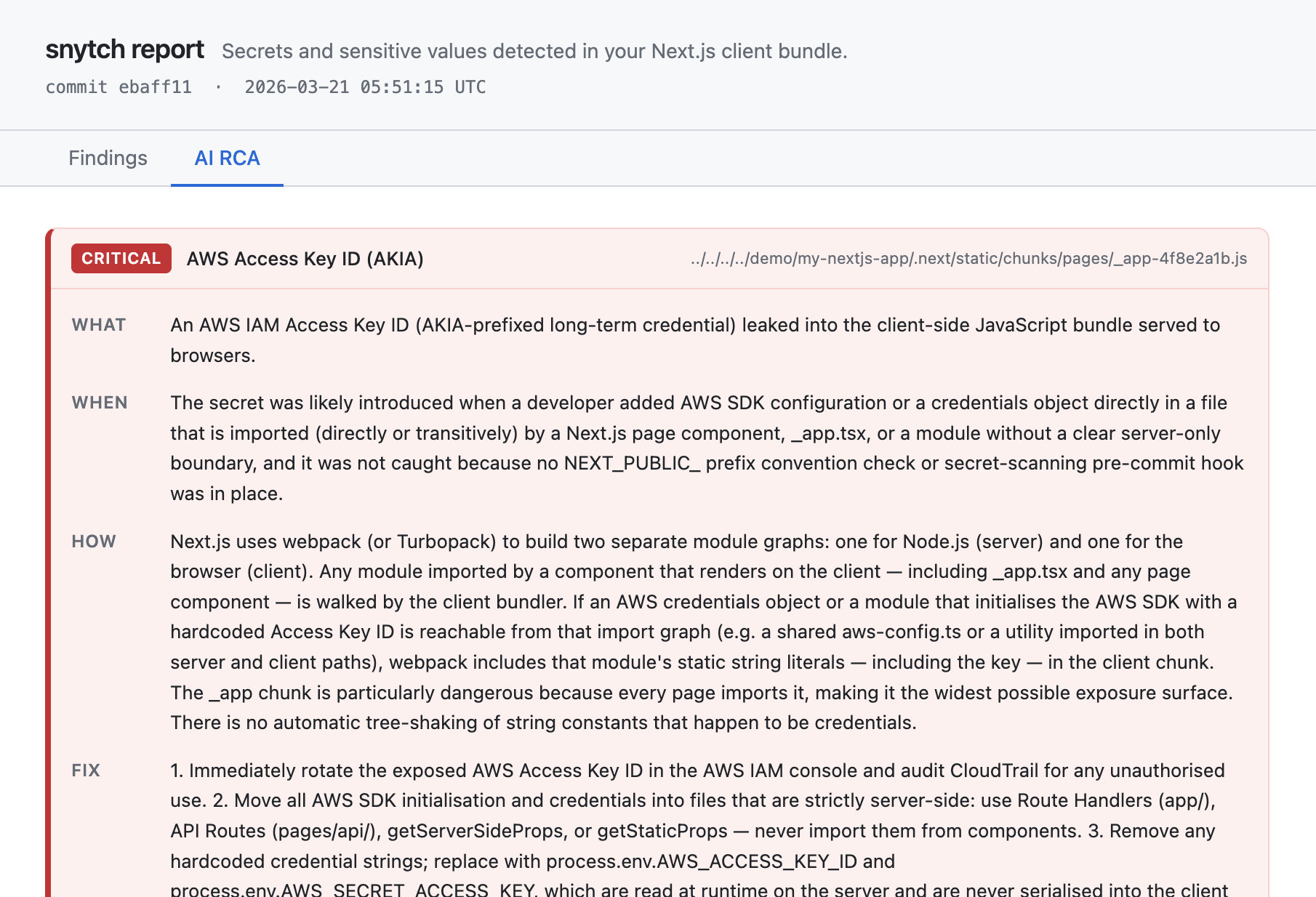
| | `snytch-reports/snytch-report.html` | Bundle scan findings with Findings and AI RCA tabs | | ||
| | `snytch-reports/snytch-check-report.html` | `NEXT_PUBLIC_` exposure findings | | ||
| | `snytch-reports/snytch-diff-report.html` | Environment variable drift across `.env` files | | ||
| | File | Contents | | ||
| | ----------------------------------------- | -------------------------------------------------- | | ||
| | `snytch-reports/snytch-report.html` | Bundle scan findings with Findings and AI RCA tabs | | ||
| | `snytch-reports/snytch-check-report.html` | `NEXT_PUBLIC_` exposure findings | | ||
| | `snytch-reports/snytch-diff-report.html` | Environment variable drift across `.env` files | | ||
@@ -155,3 +155,3 @@ > Add this to your `.gitignore` to avoid committing the reports directory: | ||
|  | ||
|  | ||
@@ -163,11 +163,15 @@ --- | ||
| - Scans `.next/static/chunks` recursively for JavaScript and CSS files | ||
| - Detects 150+ secret patterns including: | ||
| - AWS access keys and credentials | ||
| - Stripe API keys (live and test) | ||
| - Database connection strings with passwords | ||
| - GitHub personal access tokens | ||
| - Slack and Twilio tokens | ||
| - Private keys (RSA, EC, OpenSSH) | ||
| - JWT tokens and bearer tokens | ||
| - API keys from major cloud providers (Google, Azure, Firebase, etc.) | ||
| - Detects 170+ secret patterns including: | ||
| - AWS access keys, session tokens, and resource ARNs | ||
| - Stripe, Square, PayPal, Braintree, and Coinbase keys | ||
| - Database connection strings (PostgreSQL, MySQL, MongoDB, Redis, Elasticsearch, and more) | ||
| - GitHub, GitLab, and Bitbucket tokens (classic and fine-grained) | ||
| - Slack, Discord, Twilio, SendGrid, Mailgun, and Postmark tokens | ||
| - Private keys (RSA, EC, DSA, OpenSSH, PGP) | ||
| - JWT tokens, OAuth tokens, and high-entropy bearer tokens | ||
| - Cloud provider keys (Google Cloud, Azure, Firebase, Cloudflare, DigitalOcean, Vercel, Heroku) | ||
| - AI and ML API keys (OpenAI, Anthropic, Cohere, Hugging Face, Replicate, Pinecone) | ||
| - Auth providers (Auth0, Okta) | ||
| - Monitoring and observability (Datadog, New Relic, Sentry, Splunk, Grafana) | ||
| - High-entropy string heuristics for unknown secret formats | ||
| - AI root cause analysis via Claude (Anthropic) or GPT-4o (OpenAI) when `--report` is set | ||
@@ -288,7 +292,7 @@ - Git provenance for each finding (source file + introducing commit) | ||
| | Platform | Path | | ||
| | -------- | ---- | | ||
| | Platform | Path | | ||
| | -------- | ----------------------------------------------------------------- | | ||
| | macOS | `~/Library/Application Support/Claude/claude_desktop_config.json` | | ||
| | Windows | `%APPDATA%\Claude\claude_desktop_config.json` | | ||
| | Linux | `~/.config/Claude/claude_desktop_config.json` | | ||
| | Windows | `%APPDATA%\Claude\claude_desktop_config.json` | | ||
| | Linux | `~/.config/Claude/claude_desktop_config.json` | | ||
@@ -295,0 +299,0 @@ 2. Add the following: |
New alerts
Shell access
Supply chain riskThis module accesses the system shell. Accessing the system shell increases the risk of executing arbitrary code.
Found 1 instance in 1 package
Dynamic require
Supply chain riskDynamic require can indicate the package is performing dangerous or unsafe dynamic code execution.
Found 1 instance in 1 package
Environment variable access
Supply chain riskPackage accesses environment variables, which may be a sign of credential stuffing or data theft.
Found 3 instances in 1 package
Filesystem access
Supply chain riskAccesses the file system, and could potentially read sensitive data.
Found 1 instance in 1 package
Long strings
Supply chain riskContains long string literals, which may be a sign of obfuscated or packed code.
Found 1 instance in 1 package
Fixed alerts
Shell access
Supply chain riskThis module accesses the system shell. Accessing the system shell increases the risk of executing arbitrary code.
Found 1 instance in 1 package
Dynamic require
Supply chain riskDynamic require can indicate the package is performing dangerous or unsafe dynamic code execution.
Found 1 instance in 1 package
Environment variable access
Supply chain riskPackage accesses environment variables, which may be a sign of credential stuffing or data theft.
Found 3 instances in 1 package
Filesystem access
Supply chain riskAccesses the file system, and could potentially read sensitive data.
Found 1 instance in 1 package
Long strings
Supply chain riskContains long string literals, which may be a sign of obfuscated or packed code.
Found 1 instance in 1 package
Improved metrics
- Total package byte prevSize
284102
0.34%- Number of lines in readme file
392
1.03%