
Security News
Crates.io Users Targeted by Phishing Emails
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
@ssfbank/push-to-repo
Advanced tools
Commit changes back to the repo from a GitLab CI job.
Uses GitLab API and by default fails quietly (if the pushed file is for example unchanged). Easy to use and flexible to configure.
GL_PRIVATE_TOKEN to your GitLab repo CI/CD variables with a valid GitLab access token as its value.npx push-to-repo -h
All options except the filename are optional(or --all-commit if run in all commit mode). Note that by default the script does not set author details to the commit which means that it will use the credentials of the user who created the access token. This means that the commits will show up in that users commit history etc. If you want to avoid this, set author name and email explicitly.
Usage: push-to-repo -f <file> [options]
Options:
-f, --file-name <filename> the file to push
-a, --all-commit Push all modified or deleted changes or new files.
-b, --branch <branch> the branch to push (default: "CI_COMMIT_BRANCH")
-m, --message <message> commit message (default: "Update <filename> [skip ci]")
-u, --base-url <url> GitLab API base URL (default: "https://gitlab.com/api/v4")
-n, --author-name Author name
-e, --author-email Author e-mail
--fail-on-error fail the job on error
-d, --debug debug (verbose) mode
-V, --version output the version number
-h, --help display help for command
This mode of commit replaces the -f flag and lets you push all easily handled changes(modified or deleted) to existing files. New files are also added. Renames and chmods are not though.
The foremost practical use case for this is the common npm package release pattern where you increment the version of package.json, commit it, then publish it to NPM, all done in CI.
Remember that this cli only pushes through the gitlab API, so your current working tree remains unchanged. Gitlab jobs will by default swallow these changes and when the next job in the pipeline starts these are gone as it continues on the same commit. One way of handling this is for any later jobs in the pipeline to be triggered by the commit message.
This goes for the regular --file-name flag as well.
This tool is intended to be used inside GitLab CI but you can test or use it locally by setting the following GitLab CI env variables: CI_PROJECT_ID, CI_PROJECT_DIR, and CI_COMMIT_BRANCH.
All contributions are welcome! Please follow the code of conduct when interacting with others. This project lives on GitLab.
Follow @Uninen on Twitter.
FAQs
Commit changes back to the repo from a GitLab CI job.
We found that @ssfbank/push-to-repo demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 4 open source maintainers collaborating on the project.
Did you know?

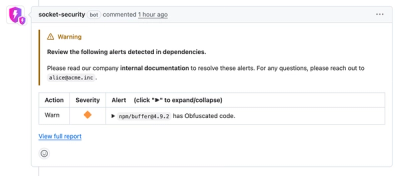
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
Product
Socket now lets you customize pull request alert headers, helping security teams share clear guidance right in PRs to speed reviews and reduce back-and-forth.

Product
Socket's Rust support is moving to Beta: all users can scan Cargo projects and generate SBOMs, including Cargo.toml-only crates, with Rust-aware supply chain checks.