@webda/elasticsearch module
This module is part of Webda Application Framework that allows you to quickly develop applications with all modern prerequisites: Security, Extensibility, GraphQL, REST, CloudNative https://webda.io






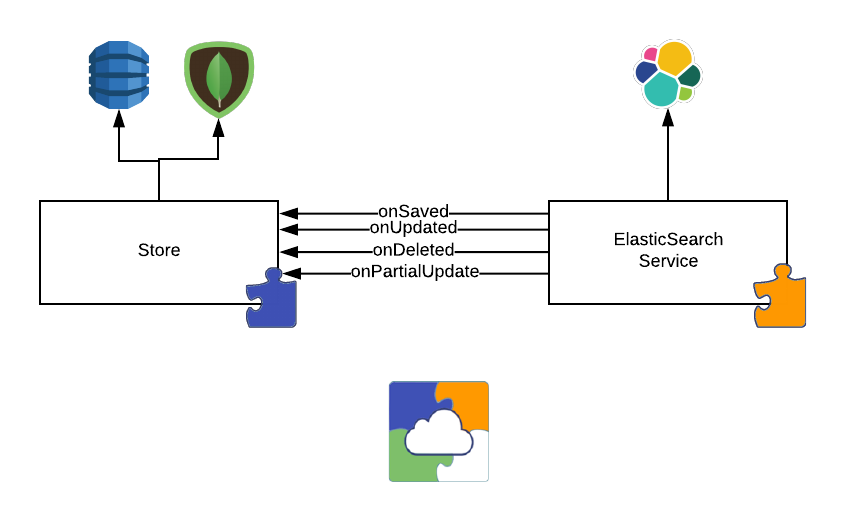
This project allows you to index all documents saved in a Webda Store by connecting to the Store event
It exposes a delete and search method for you to run queries.
Arize AI is a machine learning observability and model monitoring platform. It helps you visualize, monitor, and explain your machine learning models. Learn more

Loopingz is a software development company that provides consulting and development services. Learn more

Tellae is an innovative consulting firm specialized in cities transportation issues. We provide our clients, both public and private, with solutions to support your strategic and operational decisions. Learn more