Product
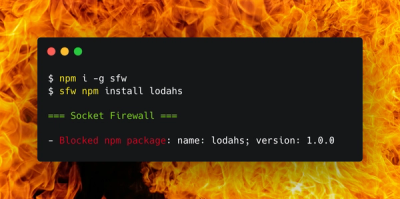
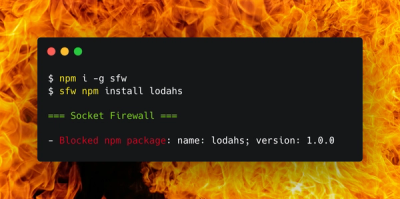
Introducing Socket Firewall: Free, Proactive Protection for Your Software Supply Chain
Socket Firewall is a free tool that blocks malicious packages at install time, giving developers proactive protection against rising supply chain attacks.
@zhike/eslint-config
Advanced tools




npm install --save-dev @zhike/eslint-config
or
yarn add -D @zhike/eslint-config
Shareable configs are designed to work with the extends feature of .eslintrc files.
You can learn more about
Shareable Configs on the
official ESLint website.
To use the Zhike JavaScript Style shareable config, first run this:
npm install --save-dev @zhike/eslint-config\
eslint-config-standard\
eslint-plugin-standard\
eslint-plugin-promise\
eslint-plugin-import\
eslint-plugin-node
eslint
Then, add this to your .eslintrc file:
{
"extends": "@zhike"
}
Note: We omitted the /eslint-config suffix since it is automatically assumed by ESLint.
You can override settings from the shareable config by adding them directly into your
.eslintrc file.
You can add a badge to your README.md file now.
With code:

It looks like
MIT. Copyright (c) Zhike.
FAQs
Zhike ESLint Shared Configuation
We found that @zhike/eslint-config demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 13 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Product
Socket Firewall is a free tool that blocks malicious packages at install time, giving developers proactive protection against rising supply chain attacks.

Research
Socket uncovers malicious Rust crates impersonating fast_log to steal Solana and Ethereum wallet keys from source code.

Research
A malicious package uses a QR code as steganography in an innovative technique.