
Security News
Crates.io Users Targeted by Phishing Emails
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
autoprefixer-stylus
Advanced tools
An autoprefixer plugin for stylus.
You can install through npm as such: npm install autoprefixer-stylus
You can include autoprefixer-stylus as a normal stylus plugin. Basic example below:
const stylus = require('stylus')
const autoprefixer = require('autoprefixer-stylus')
stylus(css)
.use(autoprefixer())
.render(function(err, output) {
console.log(output)
})
This plugin also takes any of the options that autoprefixer normally takes. Example with overrideBrowswerslist below:
stylus(css).use(autoprefixer({ overrideBrowserslist: ['ie 7', 'ie 8'] }))
By default, this plugin will display any warnings. You can disable this with the hideWarnings option. Example below:
stylus(css)
.use(autoprefixer({ hideWarnings: true });
If you'd like to install globally and run from the command line, you can do it like this:
npm install -g autoprefixer-stylus
stylus -u autoprefixer-stylus -c example.styl
FAQs
autoprefixer for stylus
The npm package autoprefixer-stylus receives a total of 7,336 weekly downloads. As such, autoprefixer-stylus popularity was classified as popular.
We found that autoprefixer-stylus demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

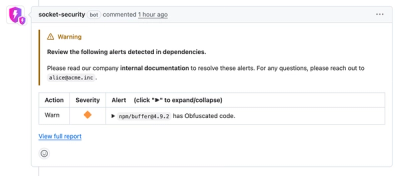
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
Product
Socket now lets you customize pull request alert headers, helping security teams share clear guidance right in PRs to speed reviews and reduce back-and-forth.

Product
Socket's Rust support is moving to Beta: all users can scan Cargo projects and generate SBOMs, including Cargo.toml-only crates, with Rust-aware supply chain checks.