
Security News
Attackers Are Hunting High-Impact Node.js Maintainers in a Coordinated Social Engineering Campaign
Multiple high-impact npm maintainers confirm they have been targeted in the same social engineering campaign that compromised Axios.
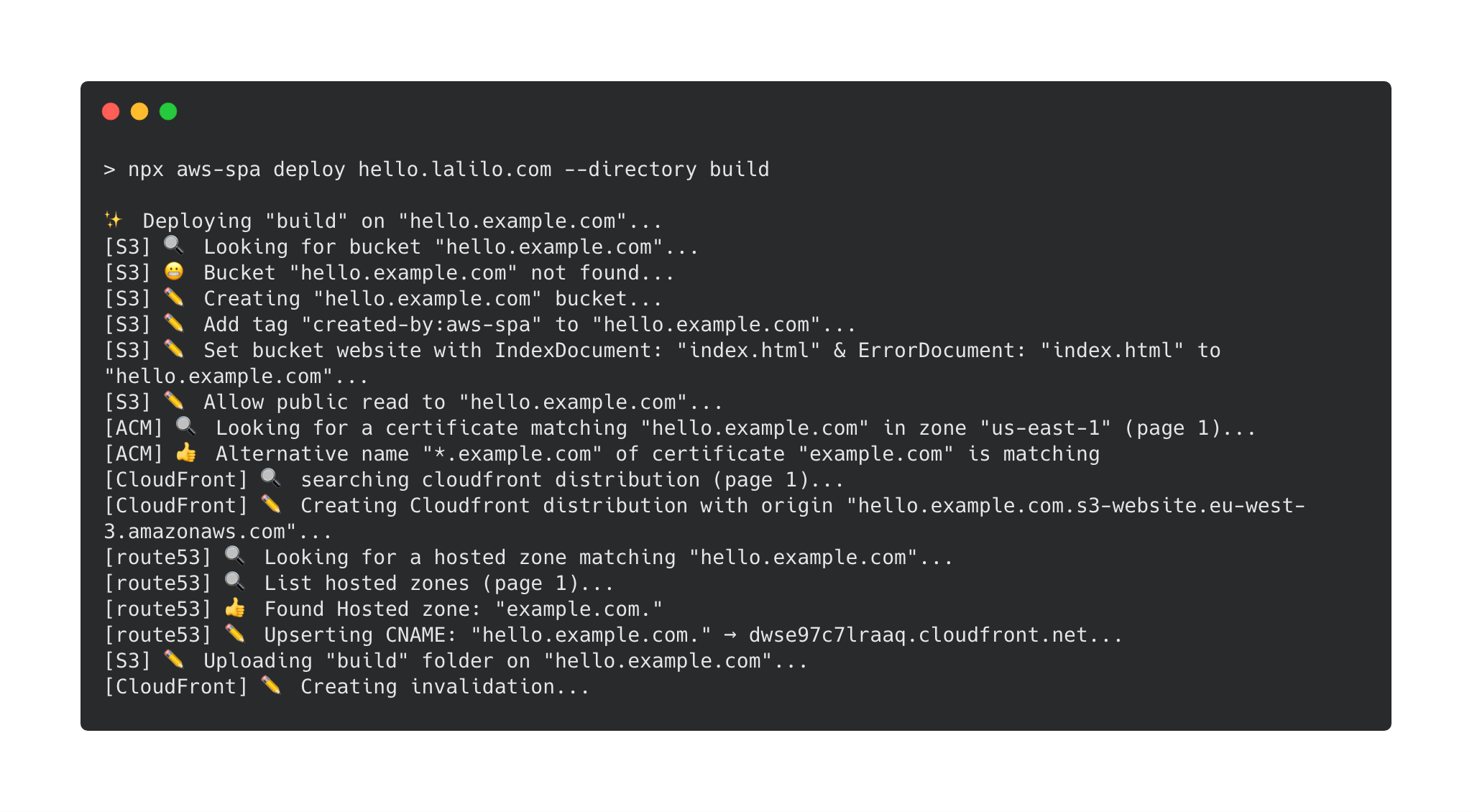
Deploy a single page app on AWS in one command.
Note: this repository is intended for internal use at Lalilo, and supports only our current deployment needs. We recommend against using it as-is in your production apps as our updates may contain breaking changes and won't be maintained to support other use cases.
npm install --dev aws-spa
npx aws-spa deploy --help
Configuring the deployment of a single page app is harder than it should be. Most SPA configuration are very similar. aws-spa embodies this idea. It is meant to handle all the quirks associated with SPA configuration.
npx create-react-app hello-world && cd hello-world
yarn add aws-spa
yarn build
# read about [create-react-app static file caching](https://facebook.github.io/create-react-app/docs/production-build#static-file-cachin)
npx aws-spa deploy hello.example.com --cacheInvalidation "index.html" --cacheBustedPrefix "static/"
Deploy a single page app on AWS
domainName:The domain name on which the SPA will be accessible. For example app.example.com.
You can also specify a path: app.example.com/something. This can be useful to deploy multiple versions of an app in the same s3 bucket. For example one could deploy a feature branch of the SPA like this:
aws-spa deploy app.example.com/$(git branch | grep * | cut -d ' ' -f2)
--wait: Wait for CloudFront distribution to be deployed & cache invalidation to be completed. If you choose not to wait (default), you won't see site changes as soon as the command ends.--directory: The directory where the static files have been generated. It must contain an index.html. Default is build.--cacheInvalidation: cache invalidation to be done in CloudFront. Default is *: all files are invalidated. For a create-react-app app you only need to invalidate /index.html--cacheBustedPrefix: a folder where files are suffixed with a hash (cash busting). Their cache-control value is set to max-age=31536000. For a create-react-app app you can specify static/.--noPrompt: Disable confirm message that prompts on non CI environments (env CI=true).--shouldBlockBucketPublicAccess: This option will deploy the SPA with a bucket not being publicly accessible. Access to the bucket will be done through an Origin Access Control (OAC). Default value is false.--noDefaultRootobject: Instead of using index.html as the root object, allows to resolve example.com/ to example.com//index.html using a cloudfront function.--redirect403ToRoot: Redirect 403 errors to the root of the SPA. This is useful if you want to use client-side routing with an S3 static website without using a hash router.--objectExpirationDays: Add a lifecycle configuration to the bucket that clean object after a number of days. This avoid having numerous outdated branch in the bucket.--viewerRequestFunctionNames: Add existing CloudFront functions as viewer-request function. Specified functions must already exist or the command will fail. If a lamdba function is already associated, the command will also fail (existing CloudFront functions will be replaced)--viewerResponseFunctionNames: Add existing CloudFront functions as viewer-response function. Specified functions must already exist or the command will fail. If a lamdba function is already associated, the command will also fail (existing CloudFront functions will be replaced)--additionalDomainNames: Specify additional domain names to assign to the CloudFront definition (in addition to the domain name).aws-spa is aware of the resources it is managing thanks to tags.
If a S3 bucket named with the domain name already exists, a prompt will ask you if you want to deleguate the management of this bucket to aws-s3 (this will basically checks that s3 bucket is well configured to serve a static website).
If a CloudFront distribution with this S3 bucket already exists, the script will fail because CloudFront distribution update is quite complicated.
managed-by-aws-spa, value: v1.cloudfront:CreateDistribution
cloudfront:ListDistributions
cloudfront:ListTagsForResource
cloudfront:TagResource
cloudfront:GetDistributionConfig
cloudfront:CreateInvalidation
cloudfront:UpdateDistribution
cloudfront:ListOriginAccessControls
cloudfront:GetOriginAccessControl
cloudfront:CreateOriginAccessControl
cloudfront:DeleteOriginAccessControl
s3:PutBucketPolicy
s3:GetBucketPolicy
s3:PutBucketWebsite
s3:GetBucketWebsite
s3:DeleteBucketWebsite
s3:PutBucketTagging
s3:GetBucketTagging
s3:DeleteBucketTagging
s3:ListBucket
s3:PutBucketPublicAccessBlock
s3:CreateBucket
s3:PutObject
s3:PutLifecycleConfiguration
s3:GetLifecycleConfiguration
route53:ListHostedZones
route53:CreateHostedZone
route53:ListResourceRecordSets
route53:ChangeResourceRecordSets
acm:ListCertificates
acm:DescribeCertificate
acm:RequestCertificate
lambda:CreateFunction
lambda:GetFunctionConfiguration
lambda:UpdateFunctionCode
lambda:UpdateFunctionConfiguration
iam:AttachRolePolicy
iam:CreateRole
iam:GetRole
If it better suits your use case, these tools are probably a very good choice because there are done for this. Meanwhile there are some reasons why it is written in javascript:
FAQs
A no-brainer script to deploy a single page app on AWS
The npm package aws-spa receives a total of 56 weekly downloads. As such, aws-spa popularity was classified as not popular.
We found that aws-spa demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 2 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Multiple high-impact npm maintainers confirm they have been targeted in the same social engineering campaign that compromised Axios.

Security News
Axios compromise traced to social engineering, showing how attacks on maintainers can bypass controls and expose the broader software supply chain.

Security News
Node.js has paused its bug bounty program after funding ended, removing payouts for vulnerability reports but keeping its security process unchanged.