
Product
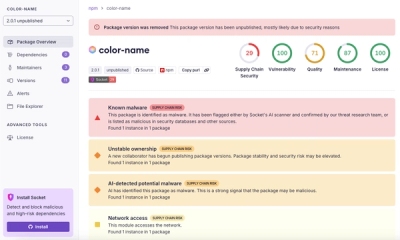
Introducing Pull Request Stories to Help Security Teams Track Supply Chain Risks
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
aws-ssm-keyring
Advanced tools
Manage Team Secrets using AWS SSM
This is a simple for managing secrets within a team.
Secrets are stored as Amazon EC2 Systems Manager parameters, and encrypted using a Amazon IAM Encryption key.
That way you can easily assign who has access the the secrets.
Create a new Encryption Key in AWS IAM. Assign users that should be allowed to access the data as admins or users of that key.
Copy the .env.dist file to .env and put the key ID in there and add your personal AWS credentials.
Run
npm i
% node dist/cli.js --help
Usage: cli [options] [command]
Options:
-h, --help output usage information
Commands:
set <id> <secret> set the secret for the given id
get <id> show the secret for the given id
delete <id> delete the secret for the given id
list list all ids for this team keyring
help [cmd] display help for [cmd]
FAQs
Manage team secrets using AWS SSM
The npm package aws-ssm-keyring receives a total of 1 weekly downloads. As such, aws-ssm-keyring popularity was classified as not popular.
We found that aws-ssm-keyring demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
Research
/Security News
npm author Qix’s account was compromised, with malicious versions of popular packages like chalk-template, color-convert, and strip-ansi published.

Research
Four npm packages disguised as cryptographic tools steal developer credentials and send them to attacker-controlled Telegram infrastructure.