
Security News
Package Maintainers Call for Improvements to GitHub’s New npm Security Plan
Maintainers back GitHub’s npm security overhaul but raise concerns about CI/CD workflows, enterprise support, and token management.
babel-preset-stage-3
Advanced tools
Babel preset for stage 3 plugins.
The gist of Stage 3 is:
Stage 3: candidate
What is it? The proposal is mostly finished and now needs feedback from implementations and users to progress further.
What’s required? The spec text must be complete. Designated reviewers (appointed by TC39, not by the champion) and the ECMAScript spec editor must sign off on the spec text. There must be at least two spec-compliant implementations (which don’t have to be enabled by default).
What’s next? Henceforth, changes should only be made in response to critical issues raised by the implementations and their use.
npm install --save-dev babel-preset-stage-3
.babelrc (Recommended).babelrc
{
"presets": ["stage-3"]
}
babel script.js --presets stage-3
require("babel-core").transform("code", {
presets: ["stage-3"]
});
FAQs
Babel preset for stage 3 plugins
The npm package babel-preset-stage-3 receives a total of 533,849 weekly downloads. As such, babel-preset-stage-3 popularity was classified as popular.
We found that babel-preset-stage-3 demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 6 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Maintainers back GitHub’s npm security overhaul but raise concerns about CI/CD workflows, enterprise support, and token management.
Product
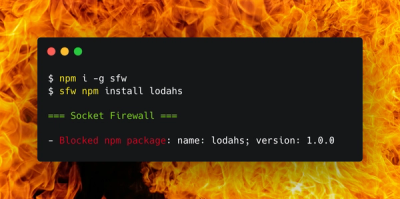
Socket Firewall is a free tool that blocks malicious packages at install time, giving developers proactive protection against rising supply chain attacks.

Research
Socket uncovers malicious Rust crates impersonating fast_log to steal Solana and Ethereum wallet keys from source code.