
Security News
Package Maintainers Call for Improvements to GitHub’s New npm Security Plan
Maintainers back GitHub’s npm security overhaul but raise concerns about CI/CD workflows, enterprise support, and token management.
Class alone.bidello is a simple class Mixin and event system.
npm install bidello
and then
import { component } from 'bidello';
class YourClass extends component() {
init() {
//...
}
}
You can extend your classes, and trigger methods by global events.
import bidello, { component } from 'bidello';
class YourClass extends component() {
onResize({ width, height }) {
}
onVisibility({ visible }) {
}
onRaf() {
}
};
// Anywhere else in your code...
bidello.trigger({ name: 'resize', fireAtStart: true }, {
width: window.innerWidth,
height: window.innerHeight,
});
bidello.trigger({ name: 'onVisibility' }, {
visible: false,
});
bidello.trigger({ name: 'raf' });
The
fireAtStartflag, if true, will force theonResizemethod to be called for any new classes created in the future (automatically passing the last known data)
Look at antipasto for a real example.
FAQs
Don't leave your Class alone
We found that bidello demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Maintainers back GitHub’s npm security overhaul but raise concerns about CI/CD workflows, enterprise support, and token management.
Product
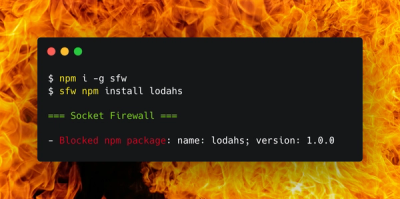
Socket Firewall is a free tool that blocks malicious packages at install time, giving developers proactive protection against rising supply chain attacks.

Research
Socket uncovers malicious Rust crates impersonating fast_log to steal Solana and Ethereum wallet keys from source code.