Research
/Security News
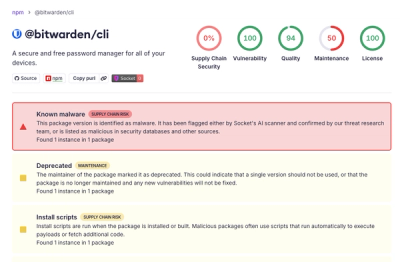
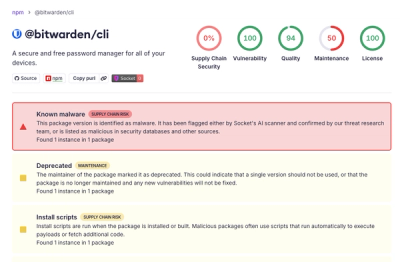
Bitwarden CLI Compromised in Ongoing Checkmarx Supply Chain Campaign
Bitwarden CLI 2026.4.0 was compromised in the Checkmarx supply chain campaign after attackers abused a GitHub Action in Bitwarden’s CI/CD pipeline.
cometd-nodejs-client
Advanced tools
Adapter code to run the CometD JavaScript library in a NodeJS environment
This project implements ES6 adapter code that allows the CometD JavaScript Client to run in NodeJS 18.x or greater.
The adapter code exports an implementation of XMLHttpRequest and WebSocket so that the CometD JavaScript Client works in NodeJS as it does within a browser environment.
WebSocket is supported via the ws package.
Install the CometD NodeJS Client:
npm install cometd-nodejs-client
import { adapt } from "cometd-nodejs-client";
import { CometD } from "cometd";
// Shim XMLHTTPRequest for Node.js (required by CometD).
adapt();
// Your normal CometD client application here.
const client = new CometD();
See here for an example CometD client application.
FAQs
Adapter code to run the CometD JavaScript library in a NodeJS environment
The npm package cometd-nodejs-client receives a total of 6,480 weekly downloads. As such, cometd-nodejs-client popularity was classified as popular.
We found that cometd-nodejs-client demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

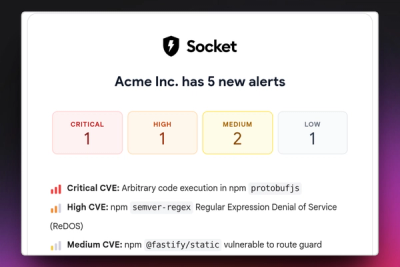
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Research
/Security News
Bitwarden CLI 2026.4.0 was compromised in the Checkmarx supply chain campaign after attackers abused a GitHub Action in Bitwarden’s CI/CD pipeline.

Research
/Security News
Docker and Socket have uncovered malicious Checkmarx KICS images and suspicious code extension releases in a broader supply chain compromise.
Product
Stay on top of alert changes with filtered subscriptions, batched summaries, and notification routing built for triage.