
Product
Introducing Socket Firewall Enterprise: Flexible, Configurable Protection for Modern Package Ecosystems
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.
connect-inject
Advanced tools
connect middleware for adding any script to the response, this is a forked version of connect-livereload.
This is a slightly modified version of connect-livereload all the credits go to the author.
For further documentation refer to the author's repo connect-livereload.
npm install connect-inject --save-dev
git clone https://github.com/danielhq/connect-inject.git
this middleware can be used to inject any sort of content into the webpage e.g. [Livereload, Weinre etc]
snippet: string | Array
snippet now accepts either string or an array.
app.use(require('connect-inject')({
snippet: "<script>alert('hello world');</script>"
}));
Options are not mandatory: app.use(require('connect-inject')());
The Options have to be provided when the middleware is loaded:
e.g.:
app.use(require('connect-inject')({
snippet: "<script>alert('hello world');</script>",
ignore: ['.js', '.svg']
}));
These are the available options with the following defaults:
// these files will be ignored
ignore: ['.js', '.css', '.svg', '.ico', '.woff', '.png', '.jpg', '.jpeg'],
// this function is used to determine if the content of `res.write` or `res.end` is html.
html: function (str) {
return /<[:_-\w\s\!\/\=\"\']+>/i.test(str);
},
// rules are provided to find the place where the snippet should be inserted.
// the main problem is that on the server side it can be tricky to determine if a string will be valid html on the client.
// the function `fn` of the first `match` is executed like this `body.replace(rule.match, rule.fn);`
// the function `fn` has got the arguments `fn(w, s)` where `w` is the matches string and `s` is the snippet.
rules: [{
match: /<\/body>/,
fn: prepend
}, {
match: /<\/html>/,
fn: prepend
}, {
match: /<\!DOCTYPE.+>/,
fn: append
}],
// snippet taks a string argument which can be anything you want, and will be appended (by default) before </body> tag
snippet: "<script>alert('hello world');</script>"
The following example is from an actual Gruntfile that uses grunt-contrib-connect
connect: {
options: {
port: 3000,
hostname: 'localhost'
},
dev: {
options: {
middleware: function (connect) {
return [
require('connect-inject')({ snippet: "<script>alert('hello world');</script>"}),
mountFolder(connect, '.tmp'),
mountFolder(connect, 'app')
];
}
}
}
}
For use as middleware in grunt simply add the following to the top of your array of middleware.
require('connect-inject')(),
You can pass in options to this call if you do not want the defaults.
dev is simply the name of the server being used with the task grunt connect:dev. The other items in the middleware array are all functions that either are of the form function (req, res, next) like checkForDownload or return that like mountFolder(connect, 'something').
You can also do multiple injections by defining a snippet inside of a rule and setting the runAll option to true
{
runAll: true,
rules: [
{
match: /<head>/ig,
snippet: '<script src="/top_file.js"></script>',
fn: function(w, s) {
return w + s;
}
},
{
match: /<script .* src=".*\.test\.js"><\/script>/ig,
snippet: [
'<script src="/bottomFile1.js"></script>',
'<script src="/bottomFile2.js"></script>',
'<script src="/src-test/testUtils.js"></script>'
]
fn: function(w, s) {
return s + w;
}
}
]
}
This is a slightly modified version of connect-livereload all the credits go to the author.
FAQs
connect middleware for adding any script to the response
We found that connect-inject demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.

Security News
Open source dashboard CNAPulse tracks CVE Numbering Authorities’ publishing activity, highlighting trends and transparency across the CVE ecosystem.
Product
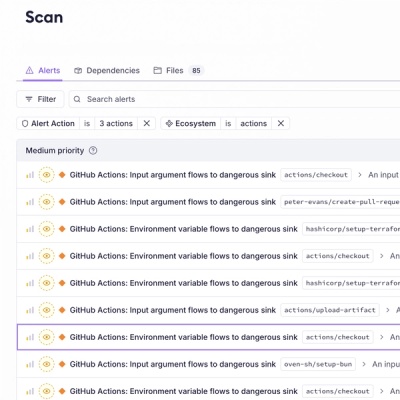
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.