
Product
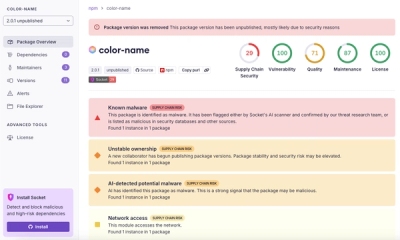
Introducing Pull Request Stories to Help Security Teams Track Supply Chain Risks
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
couchdb-connection
Advanced tools
To install run npm i couchdb-connection -g
Once installed go to the desired directory and run couchdb-connection
There will be a new folder 'couchdb-connection' with a file.js
You can also run couchdb-connection [folder name] which will create a folder with that name
Configurations
Change the user and password to your configured couchdb credentials
Then change the const db where it says 'Database Name'
If you want to change to port where the web server listens change the const port
To run the file.js you can use 'node file.js' in the terminal just remember to be in the right directory
Express docs - https://www.npmjs.com/package/express
Nano docs - https://www.npmjs.com/package/nano
FAQs
To install run npm i couchdb-connection -g
We found that couchdb-connection demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
Research
/Security News
npm author Qix’s account was compromised, with malicious versions of popular packages like chalk-template, color-convert, and strip-ansi published.

Research
Four npm packages disguised as cryptographic tools steal developer credentials and send them to attacker-controlled Telegram infrastructure.