Product
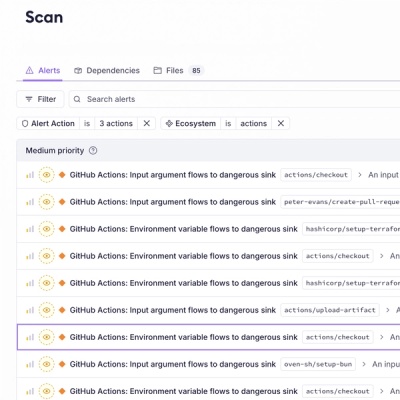
Introducing GitHub Actions Scanning Support
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.
Cypress' DOM helpers for everyone else!
const { isVisible } = require("cydom");
// or
import { isVisible } from "cydom";
Includes what Typescript definitions Cypress has as well!
Refer to https://docs.cypress.io/api/cypress-api/dom.html for documentation.
A nasty build script that extracts the DOM helpers from Cypress' monorepo and fiddles a bit to get them to import fine outside that context
Cause they are fantastic! Cypress has put an immense amount of work into identifying all the little corner cases that render tests flakey. We can stand on their very high shoulders!
Thanks to Cypress for publishing their code at all and for MIT licensing it so this kind of thing is possible. <3
FAQs
Cypress' DOM helpers outside Cypress
The npm package cydom receives a total of 10 weekly downloads. As such, cydom popularity was classified as not popular.
We found that cydom demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Product
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.
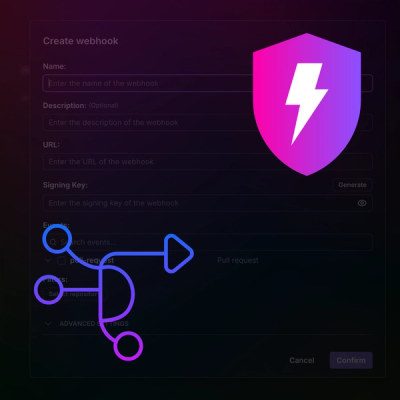
Product
Add real-time Socket webhook events to your workflows to automatically receive pull request scan results and security alerts in real time.

Research
The Socket Threat Research Team uncovered malicious NuGet packages typosquatting the popular Nethereum project to steal wallet keys.