
Security News
PodRocket Podcast: Inside the Recent npm Supply Chain Attacks
Socket CEO Feross Aboukhadijeh discusses the recent npm supply chain attacks on PodRocket, covering novel attack vectors and how developers can protect themselves.
egg-i18next
Advanced tools
[![NPM version][npm-image]][npm-url] [![build status][travis-image]][travis-url] [![Test coverage][codecov-image]][codecov-url] [![David deps][david-image]][david-url] [![Known Vulnerabilities][snyk-image]][snyk-url] [![npm download][download-image]][down
$ npm i egg-i18next --save
// {app_root}/config/plugin.js
exports.i18next = {
enable: true,
package: 'egg-i18next',
};
// {app_root}/config/config.default.js
exports.i18next = {
queryField: 'locale',
cookieField: 'locale',
cookieMaxAge: 365 * 24 * 60 * 60 * 1000, // 1 year
loadPath: '/config/locale/{{lng}}.yml',
init: { // initialization config for i18next, refer to https://www.i18next.com/configuration-options.html for more details.
fallbackLng: 'en-US',
},
};
see config/config.default.js for more detail.
Please open an issue here.
FAQs
[![NPM version][npm-image]][npm-url] [![build status][travis-image]][travis-url] [![Test coverage][codecov-image]][codecov-url] [![David deps][david-image]][david-url] [![Known Vulnerabilities][snyk-image]][snyk-url] [![npm download][download-image]][down
We found that egg-i18next demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Socket CEO Feross Aboukhadijeh discusses the recent npm supply chain attacks on PodRocket, covering novel attack vectors and how developers can protect themselves.

Security News
Maintainers back GitHub’s npm security overhaul but raise concerns about CI/CD workflows, enterprise support, and token management.
Product
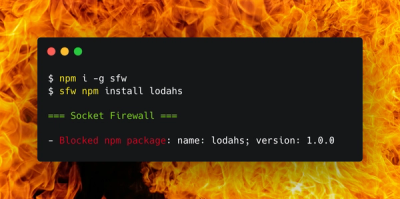
Socket Firewall is a free tool that blocks malicious packages at install time, giving developers proactive protection against rising supply chain attacks.