Research
/Security News
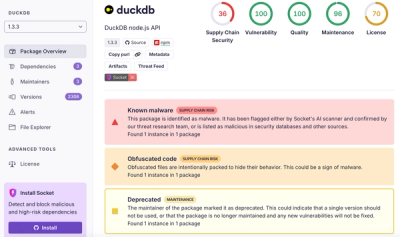
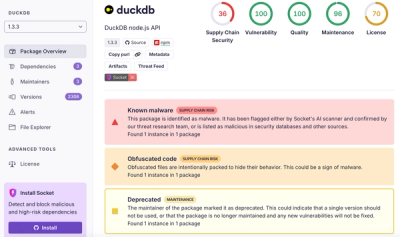
DuckDB npm Account Compromised in Continuing Supply Chain Attack
Ongoing npm supply chain attack spreads to DuckDB: multiple packages compromised with the same wallet-drainer malware.
eslint-config-oniyi
Advanced tools
JavaScript Style Guide based on airbnb/base
This style guide is based on the airbnb/base javascript style
for node.js development.
Also, some customizations are inspired by Roman Krejčík's
article.
In addition, this package ships with ava eslint rules for **/*.test.js files
[2, ['callback', 'next']]Force developers to return when they call a callback function. This is following RisingStack's recommendations on Node.js Best Practices
[2, '^.*(e|E)rr']Always check for errors in callbacks - to round-up the callback convention
[1, 120, 2, {ignoreComments: true}]Sometimes, a rule in the editor is just not enough. This rule raises a warning if a code line is
longer than 120 characters (while comments are ignored)
['error', { functions: false, classes: true, variables: true }]disallow use of variables and classes but not functions before they are defined.
Also see Risingstack's Post on clean code.
Our default export lints ES2016 and below, only requires eslint.
Check node.green for your node's version compatibility with ES2016.
npm install --save-dev eslint-config-oniyi eslint"extends": "oniyi" to your .eslintrc.jsFAQs
JavaScript Style Guide based on airbnb/javascript base
The npm package eslint-config-oniyi receives a total of 35 weekly downloads. As such, eslint-config-oniyi popularity was classified as not popular.
We found that eslint-config-oniyi demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Research
/Security News
Ongoing npm supply chain attack spreads to DuckDB: multiple packages compromised with the same wallet-drainer malware.

Security News
The MCP Steering Committee has launched the official MCP Registry in preview, a central hub for discovering and publishing MCP servers.

Product
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.