
Product
Introducing Reachability for PHP
Reachability analysis for PHP is now available in experimental, helping teams identify which vulnerabilities are actually exploitable.
eslint-json-compat-utils
Advanced tools
A utility that converts rules made for checking the AST of `jsonc-eslint-parser` into rules compatible with `@eslint/json`.
A utility that converts rules made for checking the AST of jsonc-eslint-parser into rules compatible with @eslint/json.
npm install eslint-json-compat-utils
import { toCompatRule } from "eslint-json-compat-utils";
export default toCompatRule({
meta: { /* ... */ },
create(context) {
return {
JSONArrayExpression: check,
};
},
})
toCompatRule(rule)Converts a rule object for jsonc-eslint-parser into a rule object for @eslint/json compatible.
toCompatPlugin(plugin)Converts a plugin object for jsonc-eslint-parser into a plugin object for @eslint/json compatible.
toCompatCreate(create)Converts a create function for jsonc-eslint-parser into a create function for @eslint/json compatible.
FAQs
A utility that converts rules made for checking the AST of `jsonc-eslint-parser` into rules compatible with `@eslint/json`.
The npm package eslint-json-compat-utils receives a total of 649,355 weekly downloads. As such, eslint-json-compat-utils popularity was classified as popular.
We found that eslint-json-compat-utils demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Reachability analysis for PHP is now available in experimental, helping teams identify which vulnerabilities are actually exploitable.

Product
Export Socket alert data to your own cloud storage in JSON, CSV, or Parquet, with flexible snapshot or incremental delivery.
Research
/Security News
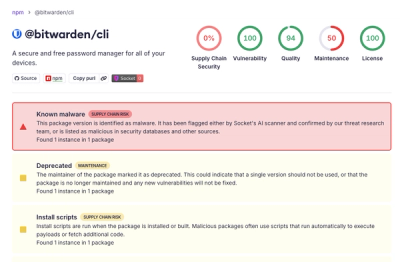
Bitwarden CLI 2026.4.0 was compromised in the Checkmarx supply chain campaign after attackers abused a GitHub Action in Bitwarden’s CI/CD pipeline.