
Security News
npm Adopts OIDC for Trusted Publishing in CI/CD Workflows
npm now supports Trusted Publishing with OIDC, enabling secure package publishing directly from CI/CD workflows without relying on long-lived tokens.
flexmonster-cli
Advanced tools
 Website: www.flexmonster.com
Website: www.flexmonster.com
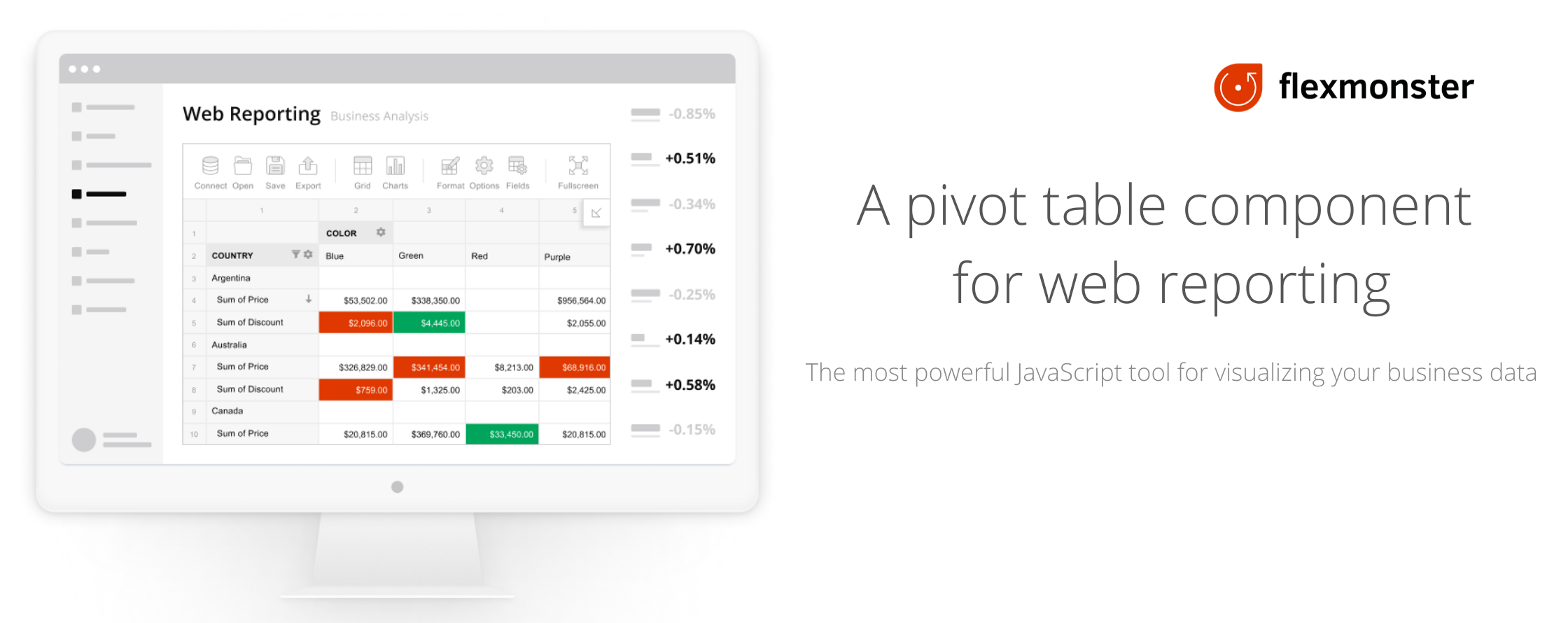
Flexmonster Pivot is a powerful JavaScript tool for interactive web reporting. It allows you to visualize and analyze data from JSON, CSV, SQL, and many more data sources quickly and conveniently. Flexmonster is designed to integrate seamlessly with any client-side framework and can be easily embedded into your application.
This npm package contains Flexmonster CLI — a command-line interface tool for Flexmonster.
The CLI can:
Install Flexmonster CLI globally to use its commands on your computer:
npm install -g flexmonster-cli
Now a new flexmonster command is available in the console.
For details on Flexmonster CLI usage, see the CLI documentation.
You can also get support from our Tech team by raising a ticket via Flexmonster Help Center.
FAQs
CLI for Flexmonster Pivot Table & Charts installation
The npm package flexmonster-cli receives a total of 97 weekly downloads. As such, flexmonster-cli popularity was classified as not popular.
We found that flexmonster-cli demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
npm now supports Trusted Publishing with OIDC, enabling secure package publishing directly from CI/CD workflows without relying on long-lived tokens.

Research
/Security News
A RubyGems malware campaign used 60 malicious packages posing as automation tools to steal credentials from social media and marketing tool users.

Security News
The CNA Scorecard ranks CVE issuers by data completeness, revealing major gaps in patch info and software identifiers across thousands of vulnerabilities.