
Security Fundamentals
Turtles, Clams, and Cyber Threat Actors: Shell Usage
The Socket Threat Research Team uncovers how threat actors weaponize shell techniques across npm, PyPI, and Go ecosystems to maintain persistence and exfiltrate data.
generator-hapi-apollo
Advanced tools
Yeoman generator for scaffolding hapi apps and plugins.
$ npm install -g yo
$ npm install -g generator-hapi-apollo
$ yo hapi-apollo:app-mongo hapi-es-club
$ cd hapi-fan-club
$ npm install
$ npm update --save
$ npm test
$ npm start
$ yo hapi-apollo:app hapi-es-club
$ cd hapi-fan-club
$ npm install
$ npm update --save
$ npm test
$ npm start
$ yo hapi-apollo:api hapi-fan-serve
$ cd hapi-fan-serve
$ npm install
$ npm update --save
$ npm test
$ npm start
$ yo hapi-apollo:web hapi-fan-site
$ cd hapi-fan-site
$ npm install
$ npm update --save
$ npm test
$ npm start
$ yo hapi-apollo:plugin hapi-space-madness
$ cd hapi-space-madness
$ npm install
$ npm update --save
$ npm test
Any issues or questions (no matter how basic), open an issue. Please take the initiative to include basic debugging information like operating system and relevant version details such as:
$ npm version
# { 'generator-hapi-apollo': '5.0.0',
# npm: '2.14.7',
# ares: '1.10.1-DEV',
# http_parser: '2.5.0',
# icu: '56.1',
# modules: '46',
# node: '4.2.2',
# openssl: '1.0.2d',
# uv: '1.7.5',
# v8: '4.5.103.35',
# zlib: '1.2.8' }
Contributions are welcome. Your code should:
If you're changing something non-trivial, you may want to submit an issue first.
:+1: All the generators include 100% test coverage.
MIT
What you create with generator-hapi-apollo is more important than generator-hapi-apollo.
FAQs
Yeoman generator for scaffolding hapi apps and plugins
We found that generator-hapi-apollo demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

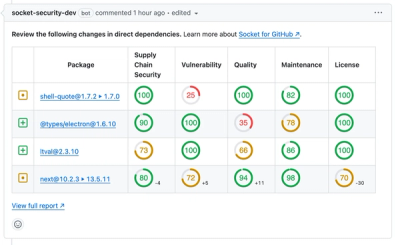
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security Fundamentals
The Socket Threat Research Team uncovers how threat actors weaponize shell techniques across npm, PyPI, and Go ecosystems to maintain persistence and exfiltrate data.

Security News
At VulnCon 2025, NIST scrapped its NVD consortium plans, admitted it can't keep up with CVEs, and outlined automation efforts amid a mounting backlog.
Product
We redesigned our GitHub PR comments to deliver clear, actionable security insights without adding noise to your workflow.