
Security News
Crates.io Users Targeted by Phishing Emails
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
generator-tabris-js
Advanced tools
A Yeoman generator for Tabris.js apps. It lets you quickly set up a new project with sensible defaults and best practices.
Install yeoman, this generator, and an HTTP server for local testing:
npm install -g yo generator-tabris-js http-server
Create your app in an empty directory:
yo tabris-js
Run the app locally:
npm start
Get the Tabris.js Developer App and point it to the URL the HTTP server has just opened (should be printed on the console).
Check out the online documentation for APIs, examples, and build documentation.
To contribute to the Yeoman generator for tabris.js, begin by cloning this repository. Once cloned you can run npm install to install the required dependencies. Next install Yeoman using npm install yo -g. Finally you can install the local copy of the tabris.js generator using npm link. With the tabris.js generator installed, you can now run yo tabris-js to start the generator.
git clone https://github.com/eclipsesource/generator-tabris-js.git
cd generator-tabris-js
npm install
npm install yo -g
npm link
You can make changes to generator and test them by using npm link. Finally, feel free to suggest changes in GitHub Issues, or send us a Pull Request.
FAQs
A Yeoman generator for Tabris.js
We found that generator-tabris-js demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 0 open source maintainers collaborating on the project.
Did you know?

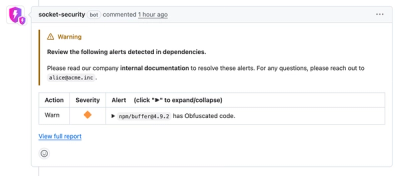
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
Product
Socket now lets you customize pull request alert headers, helping security teams share clear guidance right in PRs to speed reviews and reduce back-and-forth.

Product
Socket's Rust support is moving to Beta: all users can scan Cargo projects and generate SBOMs, including Cargo.toml-only crates, with Rust-aware supply chain checks.