
Product
Introducing Socket Firewall Enterprise: Flexible, Configurable Protection for Modern Package Ecosystems
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.
graphql-rate-limit
Advanced tools
A GraphQL Rate Limiter to add basic but granular rate limiting to your Queries or Mutations.
max per window argumentsyarn add graphql-rate-limit
import { createRateLimitDirective } from 'graphql-rate-limit';
// Step 1: get rate limit directive instance
const rateLimitDirective = createRateLimitDirective({ identifyContext: (ctx) => ctx.id });
const schema = makeExecutableSchema({
schemaDirectives: {
rateLimit: rateLimitDirective
},
resolvers: {
Query: {
getItems: () => [{ id: '1' }]
}
},
typeDefs: gql`
directive @rateLimit(
max: Int,
window: String,
message: String,
identityArgs: [String],
arrayLengthField: String
) on FIELD_DEFINITION
type Query {
# Step 2: Apply the rate limit instance to the field with config
getItems: [Item] @rateLimit(window: "1s", max: 5, message: "You are doing that too often.")
}
`
});
import { createRateLimitRule } from 'graphql-rate-limit';
// Step 1: get rate limit shield instance rule
const rateLimitRule = createRateLimitRule({ identifyContext: (ctx) => ctx.id });
const permissions = shield({
Query: {
// Step 2: Apply the rate limit rule instance to the field with config
getItems: rateLimitRule({ window: "1s", max: 5 })
}
});
const schema = applyMiddleware(
makeExecutableSchema({
typeDefs: gql`
type Query {
getItems: [Item]
}
`,
resolvers: {
Query: {
getItems: () => [{ id: '1' }]
}
}
}),
permissions
)
import { getGraphQLRateLimiter } from 'graphql-rate-limit';
// Step 1: get rate limit directive instance
const rateLimiter = getGraphQLRateLimiter({ identifyContext: (ctx) => ctx.id });
const schema = makeExecutableSchema({
typeDefs: `
type Query {
getItems: [Item]
}
`,
resolvers: {
Query: {
getItems: async (parent, args, context, info) => {
// Step 2: Apply the rate limit logic instance to the field with config
const errorMessage = await rateLimiter(
{ parent, args, context, info },
{ max: 5, window: '10s' }
);
if (errorMessage) throw new Error(errorMessage);
return [{ id: '1' }]
}
}
}
})
You'll notice that each usage example has two steps, step 1 we get an instace of a rate limiter and step 2 we apply the rate limit to one or more fields. When creating the initial instance we pass 'Instance Config' (e.g. identifyContext or a store instance), this instance will likely be the only instance you'd create for your entire GraphQL backend and can be applied to multiple fields.
Once you have your rate limiting instance you'll apply it to all the fields that require rate limiting, at this point you'll pass field level rate limiting config (e.g. window and max).
And so... we have the same 'Instance Config' and 'Field Config' options which ever way you use this library.
identifyContextA required key and used to identify the user/client. The most likely cases are either using the context's request.ip, or the user ID on the context. A function that accepts the context and returns a string that is used to identify the user.
identifyContext: (ctx) => ctx.user.id
storeAn optional key as it defaults to an InMemoryStore. See the implementation of InMemoryStore if you'd like to implement your own with your own database.
store: new MyCustomStore()
formatErrorGenerate a custom error message. Note that the message passed in to the field config will be used if its set.
formatError: ({ fieldName }) => `Woah there, you are doing way too much ${fieldName}`
createErrorGenerate a custom error. By default, a RateLimitError instance is created when a request is blocked. To return an instance of a different error class, you can return your own error using this field.
createError: (message: string) => new ApolloError(message, '429');
enableBatchRequestCacheThis enables a per-request synchronous cache to properly rate limit batch queries. Defaults to false to preserve backwards compatibility.
enableBatchRequestCache: false | true
windowSpecify a time interval window that the max number of requests can access the field. We use Zeit's ms to parse the window arg, docs here.
maxDefine the max number of calls to the given field per window.
identityArgsIf you wanted to limit the requests to a field per id, per user, use identityArgs to define how the request should be identified. For example you'd provide just ["id"] if you wanted to rate limit the access to a field by id. We use Lodash's get to access nested identity args, docs here.
messageA custom message per field. Note you can also use formatError to customise the default error message if you don't want to define a single message per rate limited field.
arrayLengthFieldLimit calls to the field, using the length of the array as the number of calls to the field.
It is recommended to use a persistent store rather than the default InMemoryStore. GraphQLRateLimit currently supports Redis as an alternative. You'll need to install Redis in your project first.
import { createRateLimitDirective, RedisStore } from 'graphql-rate-limit';
const GraphQLRateLimit = createRateLimitDirective({
identifyContext: ctx => ctx.user.id,
/**
* Import the class from graphql-rate-limit and pass in an instance of redis client to the constructor
*/
store: new RedisStore(redis.createClient())
});
FAQs
Add Rate Limiting To Your GraphQL Resolvers 💂♀
We found that graphql-rate-limit demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.

Security News
Open source dashboard CNAPulse tracks CVE Numbering Authorities’ publishing activity, highlighting trends and transparency across the CVE ecosystem.
Product
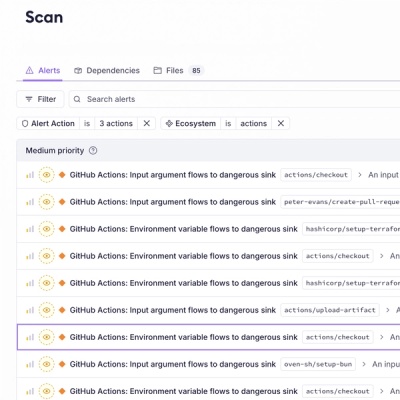
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.