
Security News
npm Adopts OIDC for Trusted Publishing in CI/CD Workflows
npm now supports Trusted Publishing with OIDC, enabling secure package publishing directly from CI/CD workflows without relying on long-lived tokens.


A simple MD2 hash function for JavaScript supports UTF-8 encoding.
You can also install js-md2 by using Bower.
bower install js-md2
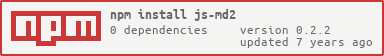
For node.js, you can use this command to install:
npm install js-md2
You could use like this:
md2('Message to hash');
If you use node.js, you should require the module first:
var md2 = require('js-md2');
If you use require.js, you should require the module first:
require(['md2.js'], function (md2) {
// ...
});
md2(''); // 8350e5a3e24c153df2275c9f80692773
md2('The quick brown fox jumps over the lazy dog'); // 03d85a0d629d2c442e987525319fc471
md2('The quick brown fox jumps over the lazy dog.'); // 71eaa7e440b611e41a6f0d97384b342a
// It also supports UTF-8 encoding
md2('中文'); // 7af93c270b0ec392ca2f0d90a927cf8a
The project is released under the MIT license.
The project's website is located at https://github.com/emn178/js-md2
Author: Chen, Yi-Cyuan (emn178@gmail.com)
v0.2.2 / 2017-02-08
root is undefined in some special environment.FAQs
A simple MD2 hash function for JavaScript supports UTF-8 encoding.
The npm package js-md2 receives a total of 3,962 weekly downloads. As such, js-md2 popularity was classified as popular.
We found that js-md2 demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
npm now supports Trusted Publishing with OIDC, enabling secure package publishing directly from CI/CD workflows without relying on long-lived tokens.

Research
/Security News
A RubyGems malware campaign used 60 malicious packages posing as automation tools to steal credentials from social media and marketing tool users.

Security News
The CNA Scorecard ranks CVE issuers by data completeness, revealing major gaps in patch info and software identifiers across thousands of vulnerabilities.