
Security News
pnpm 10.16 Adds New Setting for Delayed Dependency Updates
pnpm's new minimumReleaseAge setting delays package updates to prevent supply chain attacks, with other tools like Taze and NCU following suit.
ng2-simple-crypt
Advanced tools
Javascript module (compatible angular2+ but not limited to) for encryption through XOR cipher method.
Useful for hiding non sensitive informations, like code obfuscations, etc...
npm i ng2-simple-crypt --save
import SimpleCrypt from 'ng2-simple-crypt';
let encodedString = SimpleCrypt.encode("my-key","You are not supposed to read this");
console.log(encodedString);// "NBZYSwQLCFlDBBFZHgxdGwoKCB0NHwpZHxxMD0UNBRBe"
let decodedString = SimpleCrypt.decode("my-key",encodedString);
console.log(decodedString);// "You are not supposed to read this"
From wikipedia:
The XOR operator is extremely common as a component in more complex ciphers. By itself, using a constant repeating key, a simple XOR cipher can trivially be broken using frequency analysis. If the content of any message can be guessed or otherwise known then the key can be revealed. Its primary merit is that it is simple to implement, and that the XOR operation is computationally inexpensive. A simple repeating XOR (i.e. using the same key for xor operation on the whole data) cipher is therefore sometimes used for hiding information in cases where no particular security is required.
FAQs
angular2 module for simple encryption through XOR cipher method
We found that ng2-simple-crypt demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

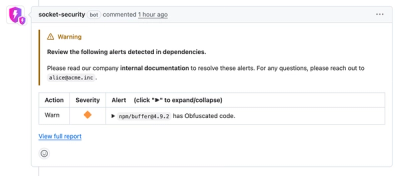
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
pnpm's new minimumReleaseAge setting delays package updates to prevent supply chain attacks, with other tools like Taze and NCU following suit.

Security News
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
Product
Socket now lets you customize pull request alert headers, helping security teams share clear guidance right in PRs to speed reviews and reduce back-and-forth.