
Product
Introducing Pull Request Stories to Help Security Teams Track Supply Chain Risks
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
h1. nodast
@nodast@ is (for now) an Asterisk FastAGI reverse proxy on "node":http://nodejs.org .
h2. How It Works
nodast receives "FastAGI":http://www.voip-info.org/wiki/view/Asterisk+FastAGI requests from "Asterisk":http://www.asterisk.org/ (or other nodast as a matter of fact), inspect incoming stream for AGI request details. Looking more specifically at the @agi_request@ parameter, the AGI URL is then matched against the config route definitions, where route definitions values are either static or dynamic. Dynamic values are simply JavaScript closure blocks, with /this/ pointing to a variable context containing all request parameters along with regexp match group items. The dynamic function is simply rewriting the AGI URL, changing the destination hostname and port as necessary. The resulting route is NOT re-injected back into route matching engine for further resolution.
Once route has been resolved, nodast then look for upstream definitions and replace logical name with upstream equivalent.
h2. Context Variables
The following list all available context variables for dynamic route definition.
$network_script
$request
$channel
$language
$type
$uniqueid
$version
$callerid
$calleridname
$callingpres
$callingani2
$callington
$callingtns
$dnid
$rdnis
$context
$extension
$priority
$enhanced
$accountcode
$threadid
h2. Sample Configuration
var config = {
listen : 9090,
upstreams : {
test : 'localhost:4573',
foobar : 'foobar.com:4573'
},
routes : {
'agi://(.*):([0-9]*)/(.*)' : function() {
if (this.$callerid === 'unknown') {
return ('agi://foobar/script/' + this.$3);
} else {
return ('agi://foobar/script/' + this.$3 + '?callerid' + this.$callerid);
}
},
'.*' : function() {
return ('agi://test/');
},
'agi://192.168.129.170:9090/' : 'agi://test/'
}
};
exports.config = config;
h2. Features
h2. Installation
h3. Git Clone
@$ git clone git://github.com/pdeschen/nodast.git@
h3. Install from npm
@$ sudo npm install nodast -g@
h3. Install the /etc/nodast config and /etc/init.d/nodast daemon script
@$ sudo nodast --install@
h2. Todo
h2. Contributors
h2. License
(The MIT License)
Copyright (c) 2011 Pascal Deschenes
Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the 'Software'), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED 'AS IS', WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
h6. Palette
F68B3A, 3AE1F6, 0697A9
FAQs
Asterisk FastAgi Proxy
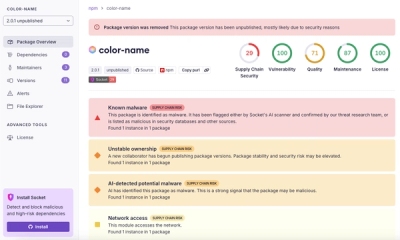
We found that nodast demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 0 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
Research
/Security News
npm author Qix’s account was compromised, with malicious versions of popular packages like chalk-template, color-convert, and strip-ansi published.

Research
Four npm packages disguised as cryptographic tools steal developer credentials and send them to attacker-controlled Telegram infrastructure.