
Product
Introducing Pull Request Stories to Help Security Teams Track Supply Chain Risks
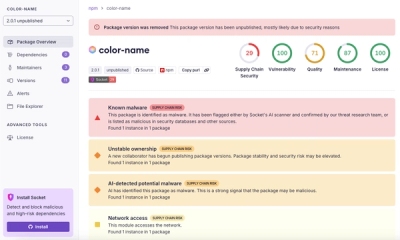
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
Google Text-to-Speech for NodeJS (Unofficial API)
npm install node-gtts
var gtts = require('node-gtts')('en');
var path = require('path');
var filepath = path.join(__dirname, 'i-love-you.wav');
gtts.save(filepath, 'I love you', function() {
console.log('save done');
})
Example with ExpressJS Router
var express = require('express');
var router = express.Router();
var gtts = require('node-gtts')('en');
router.get('/speech', function(req, res) {
res.set({'Content-Type': 'audio/mpeg'});
gtts.stream(req.query.text).pipe(res);
})
var gtts = require('node-gtts')('en');
gtts.createServer(8668);
# create file: helllo-world.wav
node-gtts en Hello World
# create server listen port 8668
# (in English by default)
node-gtts serve 8668 en
GET /?text={your-text}
GET /?text={your-text}?lang={lang}
FAQs
Google Text-to-Speech for NodeJS (Unofficial API)
We found that node-gtts demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
Research
/Security News
npm author Qix’s account was compromised, with malicious versions of popular packages like chalk-template, color-convert, and strip-ansi published.

Research
Four npm packages disguised as cryptographic tools steal developer credentials and send them to attacker-controlled Telegram infrastructure.