
Security News
Crates.io Users Targeted by Phishing Emails
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
poly-socketio
Advanced tools
Polyglot SocketIO server that allows cross-language communication via JSON
Polyglot SocketIO server that allows cross-language communication via JSON
npm i --save poly-socketio
This is used in AIVA to communicate JSON data among the Nodejs, Python and Ruby runtimes.
const polyIO = require('poly-socketio')
const IOPORT = 6466
var ioPromise = polyIO.server({port: IOPORT, clientCount: 1, timeoutMs: 15000, debug: false})
polyIO.client({port: IOPORT}) // this exposes a global.client
var msg = {
input: 'hello js',
to: 'echo.js',
intent: 'ping'
}
global.client.pass(msg)
.then((reply) => {
if (reply.output === 'ping hello js') {
console.log('success!')
} else {
console.log('error')
}
})
FAQs
Polyglot SocketIO server that allows cross-language communication via JSON
We found that poly-socketio demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

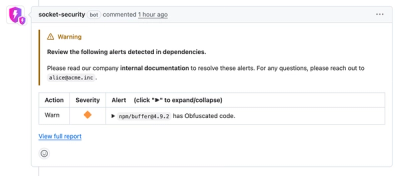
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
Product
Socket now lets you customize pull request alert headers, helping security teams share clear guidance right in PRs to speed reviews and reduce back-and-forth.

Product
Socket's Rust support is moving to Beta: all users can scan Cargo projects and generate SBOMs, including Cargo.toml-only crates, with Rust-aware supply chain checks.