
Product
Introducing Socket Firewall Enterprise: Flexible, Configurable Protection for Modern Package Ecosystems
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.
vk-api-util
Advanced tools
Utility methods for working with VK API
$ npm install --save vk-api-util
var vkUtil = require('vk-api-util');
vkUtil.bitMask(['friends', 'photos']);
//=> 6
booleanReturns true if given metod is mentioned in VK API docs.
Required
Type: string
booleanReturns true if given method doesn't require authentication.
Required
Type: string
numberReturns bit mask for given scope.
Required
Type: string, array or number
Pass a string of scopes divided by comma (,) or array of scopes. If number is passed it assumed to be a bit mask itself and returned without changes.
booleanReturns true if given area is visible within given scope.
vkApiUtil.checkScope(['friends', 'video'], 4456466);
//=> true
Required
Type: string, array or number
Required
Type: string, array or number
area and scope arguments are same as scope in aforementioned vkUtil.bitMask() method.
booleanReturns true if given method is reachable within given scope.
Required
Type: string
Type: string, array or number
Default: 0
MIT © Dmitriy Sobolev
FAQs
Utility methods for working with VK API
We found that vk-api-util demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.

Security News
Open source dashboard CNAPulse tracks CVE Numbering Authorities’ publishing activity, highlighting trends and transparency across the CVE ecosystem.
Product
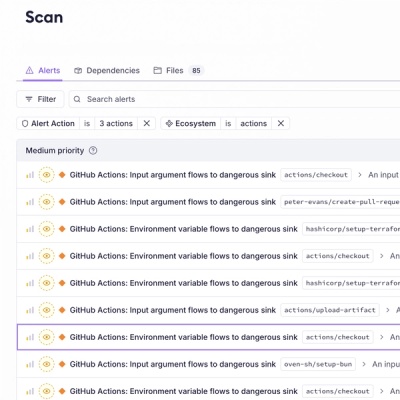
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.