
Product
Introducing Socket Firewall Enterprise: Flexible, Configurable Protection for Modern Package Ecosystems
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.
Waveform generator for superconducting circuits.
pip install bosing
Docs are hosted on Read the Docs
Examples can be found in examples.
import matplotlib.pyplot as plt
from bosing import Barrier, Channel, Hann, Play, Stack, generate_waveforms
channels = {"xy": Channel(30e6, 2e9, 1000)}
shapes = {"hann": Hann()}
schedule = Stack(duration=500e-9).with_children(
Play(
channel_id="xy",
shape_id="hann",
amplitude=0.3,
width=100e-9,
plateau=200e-9,
),
Barrier(duration=10e-9),
)
result = generate_waveforms(channels, shapes, schedule)
w = result["xy"]
plt.plot(w[0], label="I")
plt.plot(w[1], label="Q")
plt.legend()
plt.show()
examples/schedule_stress.py (0.15 s) vs benches/naive.py (1.4 s)
CPU: AMD Ryzen 5 5600
git clone https://github.com/kahojyun/Bosing.git
cd Bosing
uv sync
uv run task makedocs # build docs
uv run task format # format rust and python code
uv run task lint # lint rust and python code
uv run task test # run cargo test and pytest
FAQs
Waveform generator for pulse sequences in quantum computing
We found that bosing demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.

Security News
Open source dashboard CNAPulse tracks CVE Numbering Authorities’ publishing activity, highlighting trends and transparency across the CVE ecosystem.
Product
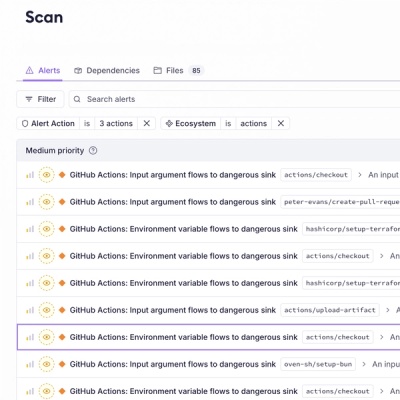
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.