Product
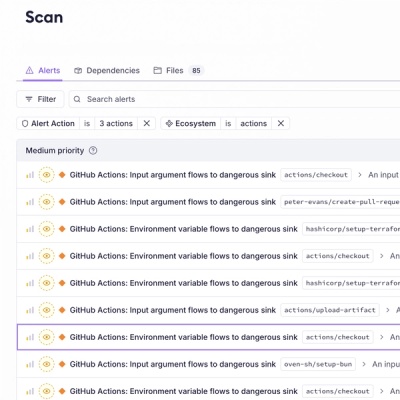
Introducing GitHub Actions Scanning Support
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.
cloud-detect
Advanced tools
cloud-detect is a Python module that determines a host's cloud provider. Highly inspired by the Go based Satellite, cloud-detect uses the same techniques (file systems and provider metadata) to properly identify cloud providers.
>>> from cloud_detect import provider
>>> provider()
'aws'
>>> provider() # when tested in local/non-supported cloud env
'unknown'
Right now the only possible responses are: 'alibaba', 'aws', 'azure', 'do', 'gcp', 'oci', 'vultr' or 'unknown'
You can get the list of supported providers using
>>> from cloud_detect import SUPPORTED_PROVIDERS
Via pip:
pip install cloud-detect
Termination-handler uses cloud-detect to keep the handling of termination notices on spot/preemptible instances cloud-agnostic, making easier to operate the same tooling in various distinct environments.
Some things that would be great to have:
FAQs
Module that determines a host's cloud provider
We found that cloud-detect demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 2 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Product
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.
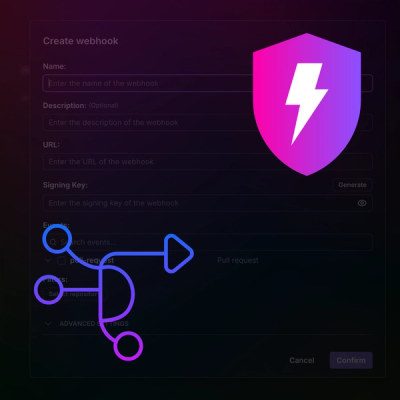
Product
Add real-time Socket webhook events to your workflows to automatically receive pull request scan results and security alerts in real time.

Research
The Socket Threat Research Team uncovered malicious NuGet packages typosquatting the popular Nethereum project to steal wallet keys.