
Security News
Meet Socket at Black Hat and DEF CON 2025 in Las Vegas
Meet Socket at Black Hat & DEF CON 2025 for 1:1s, insider security talks at Allegiant Stadium, and a private dinner with top minds in software supply chain security.
This library provides LDAP3 integration for Django, its purpose is to wrap the ldap3 library and provide useful helpers for searching and manipulating a given directory.
This library intends on becoming a full-fledged authentication backend for Django in coming updates.
$ pip install django-ldap
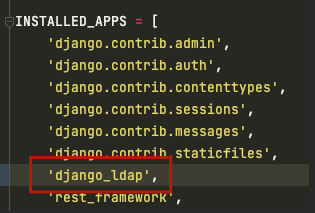
Add "django_ldap" to your INSTALLED_APPS setting
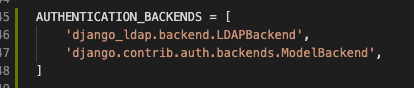
Add "django_ldap.backend.LDAPBackend" as an AUTHENTICATION_BACKENDS i.e.
AUTHENTICATION_BACKENDS = [
# ...
'django_ldap.backend.LDAPBackend',
# ...
]
LDAP_HOST = "LDAP://<LDAP_SERVER_HOSTNAME>:<LDAP_SERVER_PORT>"| Key Name | Value Default | Description | Sample |
|---|---|---|---|
| LDAP_HOST | "ldap://localhost:389" | LDAP Server FDQN | LDAP_HOST = "LDAP://localhost:389" |
| LDAP_TLS | False | Whether to enable secure ldap (note, LDAP and appropriate port should be used in hostname i.e. 636) | LDAP_TLS = False |
| LDAP_TLS_VALIDATE | ssl.CERT_OPTIONAL | If TLS is enabled then the relevant SSL verification code required (either via ssl enum or int) | LDAP_TLS_VALIDATE = ssl.CERT_OPTIONAL |
| LDAP_TLS_VERSION | ssl.PROTOCOL_TLSv1 | If TLS is enabled then the relevant TLS version must be provided | LDAP_TLS_VERSION = False |
| LDAP_BIND_USER_DN | None | DN of Auth User (None for anonymous) | LDAP_BIND_USER_DN = "cn=admin,dc=example,dc=com" |
| LDAP_BIND_PASS | None | Auth User Password (ignored if user DN is None) | LDAP_BIND_PASS = "Foo" |
| LDAP_PAGE_SIZE | 500 | Number of elements to return per paged result | LDAP_PAGE_SIZE = 500 |
| LDAP_SEARCH_ROOT | "dc=example,dc=com" | LDAP tree root (Used for search when left as default) | LDAP_SEARCH_ROOT = "dc=example,dc=com" |
| LDAP_ENABLE_REF_CACHE | True | Enables Referral Cache | LDAP_ENABLE_REF_CACHE = True |
| LDAP_SET_LDAP3_ARGS | {} | Allows LDAP3 global parameters to be updated (see LDAP3 Global Config ) | LDAP_SET_LDAP3_ARGS = {'SOCKET_SIZE': 4096} |
| LDAP_AUTH_MODE | None | NTLM for Active Directory, SASL for external cert or kerberos, leave as None for other cases, ldap3 will auto choose SIMPLE or ANONYMOUS auth | LDAP_AUTH_MODE = NTLM |
TBD
ensure black formatter is used
FAQs
Django LDAP3.
We found that django-ldap demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Meet Socket at Black Hat & DEF CON 2025 for 1:1s, insider security talks at Allegiant Stadium, and a private dinner with top minds in software supply chain security.
Security News
CAI is a new open source AI framework that automates penetration testing tasks like scanning and exploitation up to 3,600× faster than humans.

Security News
Deno 2.4 brings back bundling, improves dependency updates and telemetry, and makes the runtime more practical for real-world JavaScript projects.