
Product
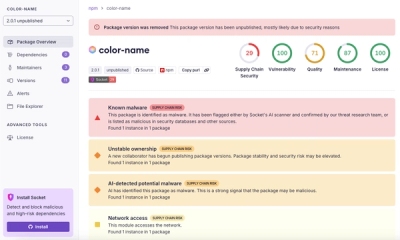
Introducing Pull Request Stories to Help Security Teams Track Supply Chain Risks
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.

Azure Entra ID Authentication for FastAPI apps made easy.
FastAPI is a modern, fast (high-performance), web framework for building APIs with Python, based on standard Python type hints.
At Intility we use FastAPI for both internal (single-tenant) and customer-facing (multi-tenant) APIs. This package enables our developers (and you 😊) to create features without worrying about authentication and authorization.
Also, we're hiring!
The documentation contains a full tutorial on how to configure Azure Entra ID and FastAPI for single- and multi-tenant applications as well as B2C apps. It includes examples on how to lock down your APIs to certain scopes, tenants, roles etc. For first time users it's strongly advised to set up your application exactly how it's described there, and then alter it to your needs later.
MIT License | Documentation | GitHub
This is a tl;dr intended to give you an idea of what this package does and how to use it. For a more in-depth tutorial and settings reference you should read the documentation.
pip install fastapi-azure-auth
# or
poetry add fastapi-azure-auth
Include swagger_ui_oauth2_redirect_url and swagger_ui_init_oauth in your FastAPI app initialization:
# file: main.py
app = FastAPI(
...
swagger_ui_oauth2_redirect_url='/oauth2-redirect',
swagger_ui_init_oauth={
'usePkceWithAuthorizationCodeGrant': True,
'clientId': settings.OPENAPI_CLIENT_ID,
},
)
Ensure you have CORS enabled for your local environment, such as http://localhost:8000.
Configure either SingleTenantAzureAuthorizationCodeBearer, MultiTenantAzureAuthorizationCodeBearer or B2CMultiTenantAuthorizationCodeBearer
# file: demoproj/api/dependencies.py
from fastapi_azure_auth.auth import SingleTenantAzureAuthorizationCodeBearer
azure_scheme = SingleTenantAzureAuthorizationCodeBearer(
app_client_id=settings.APP_CLIENT_ID,
tenant_id=settings.TENANT_ID,
scopes={
f'api://{settings.APP_CLIENT_ID}/user_impersonation': 'user_impersonation',
}
)
or for multi-tenant applications:
# file: demoproj/api/dependencies.py
from fastapi_azure_auth.auth import MultiTenantAzureAuthorizationCodeBearer
azure_scheme = MultiTenantAzureAuthorizationCodeBearer(
app_client_id=settings.APP_CLIENT_ID,
scopes={
f'api://{settings.APP_CLIENT_ID}/user_impersonation': 'user_impersonation',
},
validate_iss=False
)
To validate the iss, configure an
iss_callable.
Add azure_scheme as a dependency for your views/routers, using either Security() or Depends().
# file: main.py
from demoproj.api.dependencies import azure_scheme
app.include_router(api_router, prefix=settings.API_V1_STR, dependencies=[Security(azure_scheme, scopes=['user_impersonation'])])
Optional but recommended.
# file: main.py
@app.on_event('startup')
async def load_config() -> None:
"""
Load OpenID config on startup.
"""
await azure_scheme.openid_config.load_config()
Your OpenAPI documentation will get an Authorize button, which can be used to authenticate.

The user can select which scopes to authenticate with, based on your configuration.

FAQs
Easy and secure implementation of Azure Entra ID for your FastAPI APIs
We found that fastapi-azure-auth demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
Research
/Security News
npm author Qix’s account was compromised, with malicious versions of popular packages like chalk-template, color-convert, and strip-ansi published.

Research
Four npm packages disguised as cryptographic tools steal developer credentials and send them to attacker-controlled Telegram infrastructure.