
Security News
MCP Steering Committee Launches Official MCP Registry in Preview
The MCP Steering Committee has launched the official MCP Registry in preview, a central hub for discovering and publishing MCP servers.
GhostWriter lets you edit a website via lektor, a flexible and powerful static content management system for building complex and beautiful websites out of flat files - for people who do not want to make a compromise between a CMS and a static blog engine.
GhostWriter lets you edit a website via lektor, a flexible and powerful static content management system for building complex and beautiful websites out of flat files - for people who do not want to make a compromise between a CMS and a static blog engine.
If you want to edit a website with the ease of a CMS and share it as static pages GhostWriter starts a lektor server locally and include some git functionalities to transparently upload your changes or retrieve updates from an upstream repository. GhostWriter also allow you to share your work via .onion, by using OnionShare or a nginx webserver running on a Docker container. Everything is always hosted on your machine, and disappear when you shutdown GhostWriter. The .onion can be accessed via Tor Browser.
FAQs
GhostWriter lets you edit a website via lektor, a flexible and powerful static content management system for building complex and beautiful websites out of flat files - for people who do not want to make a compromise between a CMS and a static blog engine.
We found that ghostwriter demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
The MCP Steering Committee has launched the official MCP Registry in preview, a central hub for discovering and publishing MCP servers.

Product
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
Research
/Security News
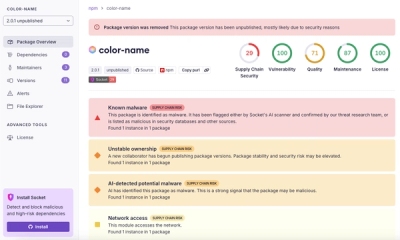
npm author Qix’s account was compromised, with malicious versions of popular packages like chalk-template, color-convert, and strip-ansi published.