Research
/Security News
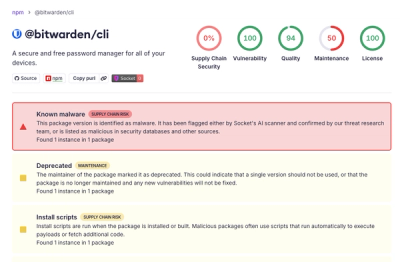
Bitwarden CLI Compromised in Ongoing Checkmarx Supply Chain Campaign
Bitwarden CLI 2026.4.0 was compromised in the Checkmarx supply chain campaign after attackers abused a GitHub Action in Bitwarden’s CI/CD pipeline.
ida-domain
Advanced tools
The IDA Domain API is a new open-source Python API designed to make scripting in IDA simpler, more consistent, and more natural.
This is a first step in a much longer journey. It’s not the finish line, but a foundation for ongoing collaboration between Hex-Rays and the reverse engineering community. Over time, the Domain API will expand to cover more areas of IDA, gradually becoming the main entry point for scripting and plugin development.
The Domain in Domain API refers to the domain of reverse engineering. Concepts like functions, types, cross-references, and more are first-class citizens in this API, giving you cleaner, domain-focused abstractions for common tasks.
The Domain API sits on top of the IDA Python SDK, complementing it rather than replacing it. You can use both side by side—combining the clarity and simplicity of Domain API calls with the full flexibility of the SDK when needed.
Compatibility: Requires IDA Pro 9.1.0 or later
pip install.IDA Pro Version: The IDA Domain library requires IDA Pro 9.1.0 or later.
Set the IDADIR environment variable to point to your IDA installation directory:
export IDADIR="[IDA Installation Directory]"
Example:
export IDADIR="/Applications/IDA Professional 9.1.app/Contents/MacOS/"
Note: If you have already installed and configured the
idaproPython package, settingIDADIRis not required.
pip install ida-domain
Here is an example showing how to use IDA Domain to analyze a binary:
#!/usr/bin/env python3
"""
Database exploration example for IDA Domain API.
This example demonstrates how to open an IDA database and explore its basic properties.
"""
import argparse
from dataclasses import asdict
import ida_domain
from ida_domain import Database
from ida_domain.database import IdaCommandOptions
def explore_database(db_path):
"""Explore basic database information."""
ida_options = IdaCommandOptions(auto_analysis=True, new_database=False)
with Database.open(db_path, ida_options) as db:
# Get basic information
print(f'Address range: {hex(db.minimum_ea)} - {hex(db.maximum_ea)}')
# Get metadata
print('Database metadata:')
metadata_dict = asdict(db.metadata)
for key, value in metadata_dict.items():
print(f' {key}: {value}')
# Count functions
function_count = 0
for _ in db.functions:
function_count += 1
print(f'Total functions: {function_count}')
def main():
"""Main entry point with argument parsing."""
parser = argparse.ArgumentParser(description='Database exploration example')
parser.add_argument(
'-f', '--input-file', help='Binary input file to be loaded', type=str, required=True
)
args = parser.parse_args()
explore_database(args.input_file)
if __name__ == '__main__':
main()
Complete documentation is available at: https://ida-domain.docs.hex-rays.com/
For development, we use a uv based workflow:
git clone https://github.com/HexRaysSA/ida-domain.git
cd ida-domain
uv sync --extra dev
uv run pre-commit install
Set the IDADIR environment variable to point to your IDA installation directory:
Run the test suite using pytest:
uv sync --extra dev
uv run pytest
To build the documentation locally:
uv sync --extra docs
uv run mkdocs serve
Or to just build it,
uv run mkdocs build
The documentation is available in site/
The latest documentation is available at: https://ida-domain.docs.hex-rays.com/
Check the examples/ directory for usage examples:
uv run python examples/analyze_database.py
We welcome contributions! Please see our Contributing Guidelines for details on how to:
This project is licensed under the MIT License - see the LICENSE file for details.
FAQs
IDA Domain API - Python interface for IDA Pro reverse engineering platform
We found that ida-domain demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 2 open source maintainers collaborating on the project.
Did you know?

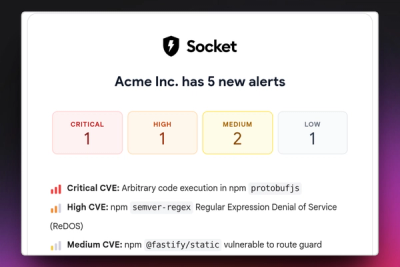
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Research
/Security News
Bitwarden CLI 2026.4.0 was compromised in the Checkmarx supply chain campaign after attackers abused a GitHub Action in Bitwarden’s CI/CD pipeline.

Research
/Security News
Docker and Socket have uncovered malicious Checkmarx KICS images and suspicious code extension releases in a broader supply chain compromise.
Product
Stay on top of alert changes with filtered subscriptions, batched summaries, and notification routing built for triage.