
Security News
pnpm 10.16 Adds New Setting for Delayed Dependency Updates
pnpm's new minimumReleaseAge setting delays package updates to prevent supply chain attacks, with other tools like Taze and NCU following suit.
joserfc is a Python library that provides a comprehensive implementation of several
essential JSON Object Signing and Encryption (JOSE) standards.
This package contains implementation of:
And draft RFCs implementation of:
A quick and simple JWT encoding and decoding would look something like this:
.. code-block:: python
>>> from joserfc import jwt
>>> from joserfc.jwk import OctKey
>>> key = OctKey.import_key("secret")
>>> encoded = jwt.encode({"alg": "HS256"}, {"k": "value"}, key)
>>> encoded
'eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJrIjoidmFsdWUifQ.ni-MJXnZHpFB_8L9P9yllj3RNDfzmD4yBKAyefSctMY'
>>> token = jwt.decode(encoded, key)
>>> token.header
{'alg': 'HS256', 'typ': 'JWT'}
>>> token.claims
{'k': 'value'}
>>> claims_requests = jwt.JWTClaimsRegistry()
>>> claims_requests.validate(token.claims)
Licensed under BSD. Please see LICENSE for licensing details.
FAQs
The ultimate Python library for JOSE RFCs, including JWS, JWE, JWK, JWA, JWT
We found that joserfc demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

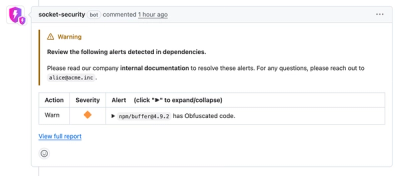
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
pnpm's new minimumReleaseAge setting delays package updates to prevent supply chain attacks, with other tools like Taze and NCU following suit.

Security News
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
Product
Socket now lets you customize pull request alert headers, helping security teams share clear guidance right in PRs to speed reviews and reduce back-and-forth.