Research
/Security News
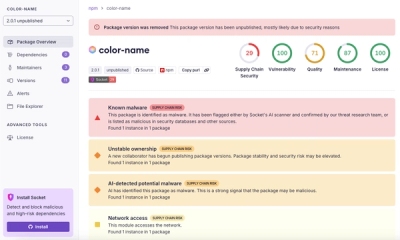
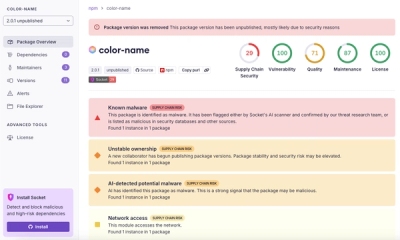
npm Author Qix Compromised via Phishing Email in Major Supply Chain Attack
npm author Qix’s account was compromised, with malicious versions of popular packages like chalk-template, color-convert, and strip-ansi published.
Mercurial is a fast, easy to use, distributed revision control tool for software developers.
Basic install::
$ make # see install targets $ make install # do a system-wide install $ hg debuginstall # sanity-check setup $ hg # see help
Running without installing::
$ make local # build for inplace usage $ ./hg --version # should show the latest version
See https://mercurial-scm.org/ for detailed installation instructions, platform-specific notes, and Mercurial user information.
Mercurial ships a copy of the python-zstandard sources. This is used to provide support for zstd compression and decompression functionality. The module is not intended to be replaced by the plain python-zstandard nor is it intended to use a system zstd library. Patches can result in hard to diagnose errors and are explicitly discouraged as unsupported configuration.
FAQs
Fast scalable distributed SCM (revision control, version control) system
We found that mercurial demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 7 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Research
/Security News
npm author Qix’s account was compromised, with malicious versions of popular packages like chalk-template, color-convert, and strip-ansi published.

Research
Four npm packages disguised as cryptographic tools steal developer credentials and send them to attacker-controlled Telegram infrastructure.

Security News
Ruby maintainers from Bundler and rbenv teams are building rv to bring Python uv's speed and unified tooling approach to Ruby development.