
Product
Introducing Data Exports
Export Socket alert data to your own cloud storage in JSON, CSV, or Parquet, with flexible snapshot or incremental delivery.
python-osc
Advanced tools
Open Sound Control server and client implementations in pure python.
.. image:: https://github.com/attwad/python-osc/actions/workflows/python-test.yml/badge.svg :target: https://github.com/attwad/python-osc/actions/workflows/python-test.yml
This library was developed following the
OpenSoundControl Specification 1.0 <https://opensoundcontrol.stanford.edu/spec-1_0.html>_
and is currently in a stable state.
Available at https://python-osc.readthedocs.io/.
python-osc is a pure python library that has no external dependencies, to install it just use pip (prefered):
.. image:: https://img.shields.io/pypi/v/python-osc.svg :target: https://pypi.python.org/pypi/python-osc
.. code-block:: bash
$ pip install python-osc
.. code-block:: python
"""Small example OSC client
This program sends 10 random values between 0.0 and 1.0 to the /filter address, waiting for 1 seconds between each value. """ import argparse import random import time
from pythonosc import udp_client
if name == "main": parser = argparse.ArgumentParser() parser.add_argument("--ip", default="127.0.0.1", help="The ip of the OSC server") parser.add_argument("--port", type=int, default=5005, help="The port the OSC server is listening on") args = parser.parse_args()
client = udp_client.SimpleUDPClient(args.ip, args.port, timeout=10)
for x in range(10):
client.send_message("/filter", random.random())
time.sleep(1)
.. code-block:: python
"""Small example OSC server
This program listens to several addresses, and prints some information about received packets. """ import argparse import math
from pythonosc.dispatcher import Dispatcher from pythonosc import osc_server
def print_volume_handler(unused_addr, args, volume): print("[{0}] ~ {1}".format(args[0], volume))
def print_compute_handler(unused_addr, args, volume): try: print("[{0}] ~ {1}".format(args[0], args1)) except ValueError: pass
if name == "main": parser = argparse.ArgumentParser() parser.add_argument("--ip", default="127.0.0.1", help="The ip to listen on") parser.add_argument("--port", type=int, default=5005, help="The port to listen on") args = parser.parse_args()
dispatcher = Dispatcher()
dispatcher.map("/filter", print)
dispatcher.map("/volume", print_volume_handler, "Volume")
dispatcher.map("/logvolume", print_compute_handler, "Log volume", math.log)
server = osc_server.ThreadingOSCUDPServer(
(args.ip, args.port), dispatcher, timeout=10)
print("Serving on {}".format(server.server_address))
server.serve_forever()
.. code-block:: python
from pythonosc import osc_bundle_builder
from pythonosc import osc_message_builder
bundle = osc_bundle_builder.OscBundleBuilder(
osc_bundle_builder.IMMEDIATELY)
msg = osc_message_builder.OscMessageBuilder(address="/SYNC")
msg.add_arg(4.0)
# Add 4 messages in the bundle, each with more arguments.
bundle.add_content(msg.build())
msg.add_arg(2)
bundle.add_content(msg.build())
msg.add_arg("value")
bundle.add_content(msg.build())
msg.add_arg(b"\x01\x02\x03")
bundle.add_content(msg.build())
sub_bundle = bundle.build()
# Now add the same bundle inside itself.
bundle.add_content(sub_bundle)
# The bundle has 5 elements in total now.
bundle = bundle.build()
# You can now send it via a client with the `.send()` method:
client.send(bundle)
Unlicensed, do what you want with it. (http://unlicense.org)
FAQs
Open Sound Control server and client implementations in pure Python
We found that python-osc demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Export Socket alert data to your own cloud storage in JSON, CSV, or Parquet, with flexible snapshot or incremental delivery.
Research
/Security News
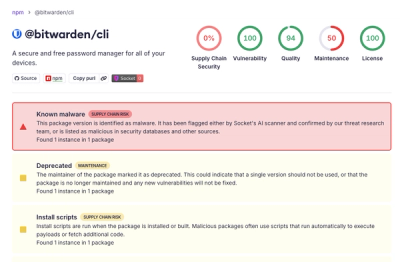
Bitwarden CLI 2026.4.0 was compromised in the Checkmarx supply chain campaign after attackers abused a GitHub Action in Bitwarden’s CI/CD pipeline.

Research
/Security News
Docker and Socket have uncovered malicious Checkmarx KICS images and suspicious code extension releases in a broader supply chain compromise.