
Research
/Security News
Intercom’s npm Package Compromised in Ongoing Mini Shai-Hulud Worm Attack
Compromised intercom-client@7.0.4 npm package is tied to the ongoing Mini Shai-Hulud worm attack targeting developer and CI/CD secrets.
sendtomail
Advanced tools
# debug settings for more information
>>> from sendtomail import *
>>> server.debug("on") #enable
>>> server.debug("off") #disable
# Send free message to email (plain)
>>> from sendtomail import *
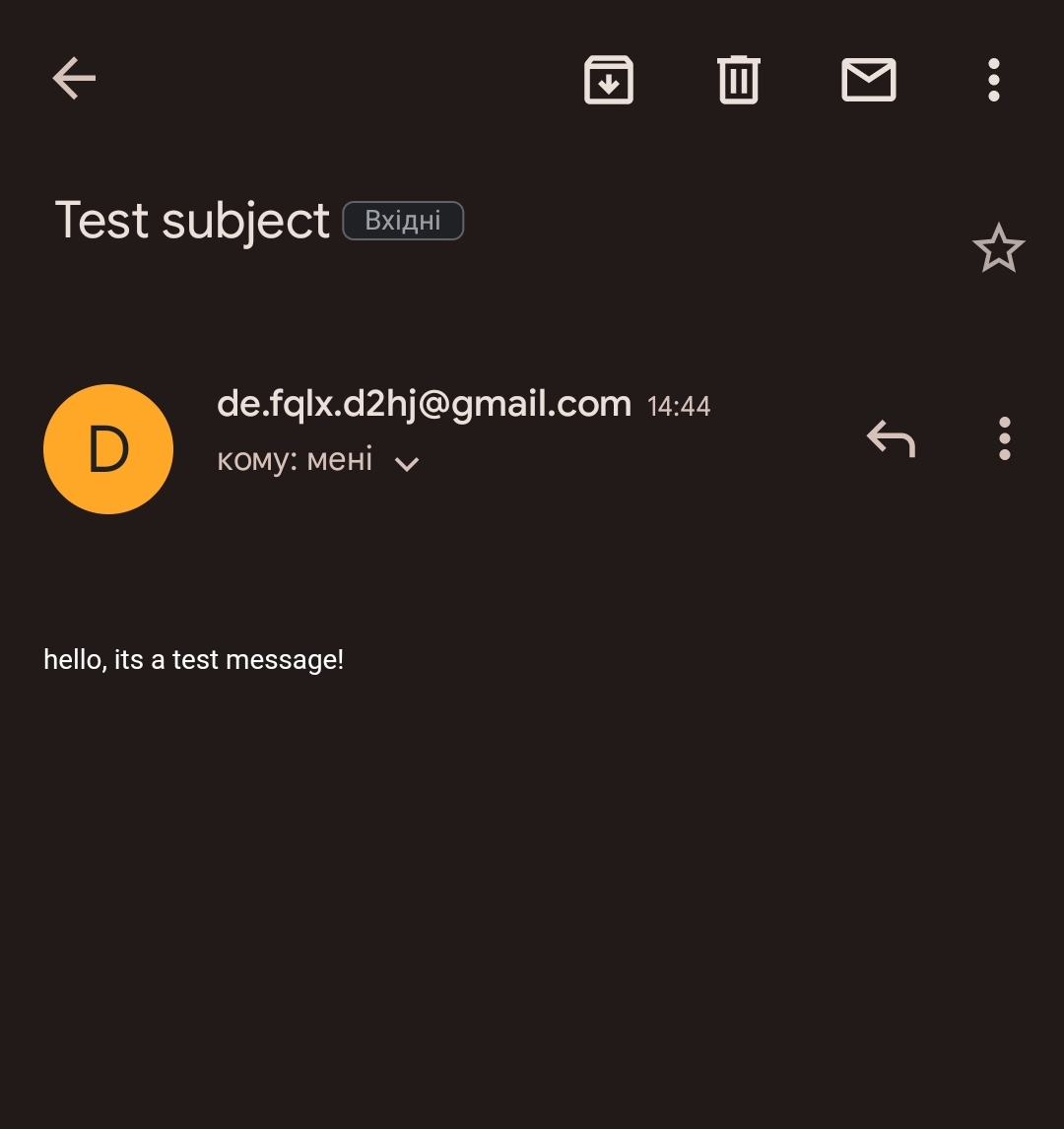
>>> server.send("gmail.com", "he1zen@null.net", "plain", "Test subject", "hello, its a test message!")
'200'
>>>
# Send free message to email (html)
>>> from sendtomail import *
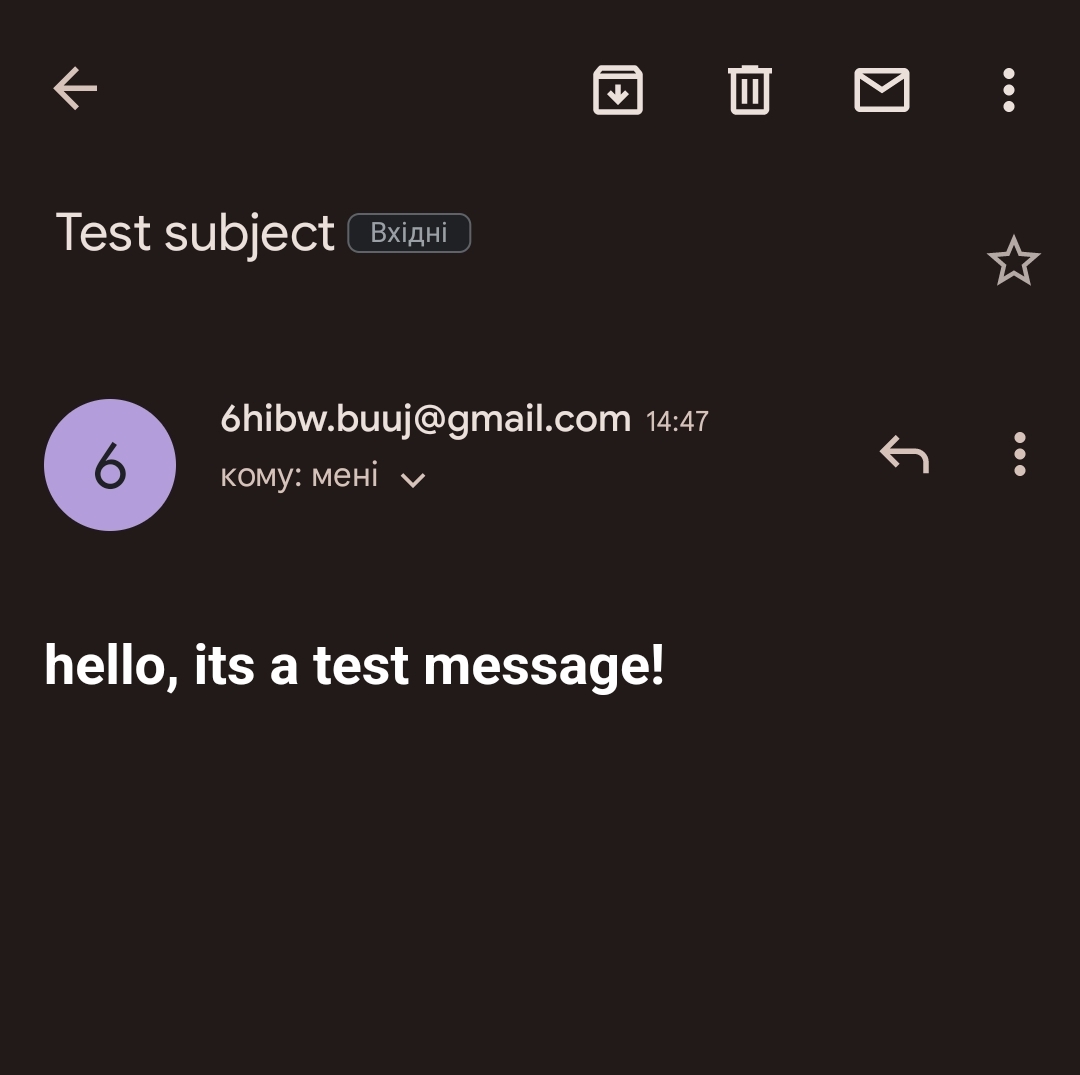
>>> server.send("gmail.com", "he1zen@null.net", "html", "Test subject",
"""<!DOCTYPE html>
<html>
<body>
<h1> hello, its a test message! </h1>
</body>
</html>""")
'200'
>>>
# Servers list
>>> from sendtomail import *
>>> regions = server.regions()
>>> print(regions)
SMTP servers: gmail.com, yandex.com, mail.ru
>>>
# Get Free SMTP, POP3, IMAP email
>>> from sendtomail import *
>>> server.mail()
{'google-mail': 'qcp9ex.iqu0@gmail.com', 'google-pass': 'dmxsdxqgvlcypitf'}
>>>
# Free email checker
>>> from sendtomail import *
>>> server.validate("he1zen@null.net")
'valid'
>>>
# Send custom data
>>> from sendtomail import *
>>> custom.data("^38^92%72^92%65^92%10")
'\nlocation : Ukraine\nServer IP : 185.16.36.136\ncreator : He1Zen, mishakorzik\nmirror : Europe, amazon\nping : 50-70ms\n'
>>>
# get server info with print
>>> from sendtomail import *
>>> server.info(False)
location: Ukraine
creator: He1Zen, mishakorzik
mirror: Europe, amazon
ping: 50-70ms
>>>
# get server info with return
>>> from sendtomail import *
>>> server.info(True)
'\nlocation : Ukraine\nServer IP : 185.16.36.136\ncreator : He1Zen, mishakorzik\nmirror : Europe, amazon\nping : 50-70ms\n'
>>>
# Create temp mail
>>> from sendtomail import tempmail
>>> tempmail.create()
'qwm5cn282k55sp@dcctb.com'
>>>
# Read last message from temp mail
>>> from sendtomail import tempmail
>>> tempmail.read("qwm5cn282k55sp", "dcctb.com")
mailbox is empty
>>>
download file sendtomail.exe - v1 download file sendtomail.exe - v2 download file sendtomail.exe - v3 download file sendtomail.exe - v4
and start file, i recommend select gmail.com server.
## Status codes
200 - Succesfully send
400 - Failed to send
401 - bad request or wrong command
403 - Email protected or secured
404 - Email not found, try another email
429 - Server error, choose another server
500 - Internal Server Error, try again later
503 - Service Unavailable, try again later
504 - Try another server
## Other codes
valid - mailbox exists
invalid - mailbox does not exist
timeout - mailbox is unknown
## Services
gmail.com - fast - recommend
yandex.com - slow - not recommend
mail.ru - slow - not recommend
there are logs on the server for security purposes
FAQs
Free SMTP email sender using virtual email address.
We found that sendtomail demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Research
/Security News
Compromised intercom-client@7.0.4 npm package is tied to the ongoing Mini Shai-Hulud worm attack targeting developer and CI/CD secrets.

Research
Socket detected a malicious supply chain attack on PyPI package lightning versions 2.6.2 and 2.6.3, which execute credential-stealing malware on import.

Research
A brand-squatted TanStack npm package used postinstall scripts to steal .env files and exfiltrate developer secrets to an attacker-controlled endpoint.