Product
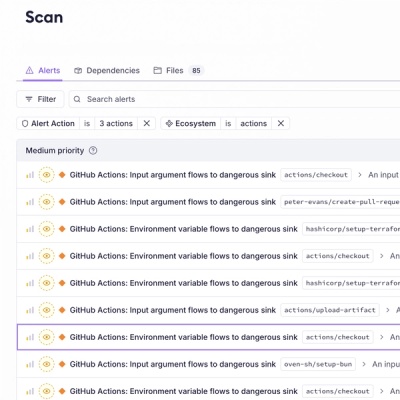
Introducing GitHub Actions Scanning Support
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.

This is the Sigma command line interface using the pySigma library to manage, list and convert Sigma rules into query languages.
The easiest way to install the Sigma CLI is via pipx or pip. For this purpose run one of the following:
python -m pipx install sigma-cli
python -m pip install sigma-cli
on macOS use
python3 -m pip install sigma-cli
Another way is to run this from source in a virtual environment managed by Poetry:
git clone https://github.com/SigmaHQ/sigma-cli.git
cd sigma-cli
poetry install
poetry shell
The CLI is available as sigma command. A typical invocation is:
sigma convert -t <backend> -p <processing pipeline 1> -p <processing pipeline 2> [...] <directory or file>
E.g. to convert process creation Sigma rules from a directory into Splunk queries for Sysmon logs run:
sigma convert -t splunk -p sysmon sigma/rules/windows/process_creation
Required backends must be installed using the following command prior to conducting conversions.
To list all available plugins run the following command:
sigma plugin list
Install a plugin of your choice with:
sigma plugin install <backend>
E.g. to install the splunk backend run:
sigma plugin install splunk
Available conversion backends and processing pipelines can be listed with sigma list.
Use -O or --backend-option for passing options to the backend as key=value pairs (-O testparam=123) .
This backend option parameter can be used multiple times (-O first=123 -O second=456).
Backends can support different output formats, e.g. plain queries and a file that can be imported into the target
system. These formats can be listed with sigma list formats <backend> and specified for conversion with the -f
option.
In addition, an output file can be specified with -o.
Example for output formats and files:
sigma convert -t splunk -f savedsearches -p sysmon -o savedsearches.conf sigma/rules/windows/process_creation
Outputs a Splunk savedsearches.conf containing the converted searches.
Backends and pipelines can be integrated by adding the corresponding packages as dependency with:
poetry add <package name>
A backend has to be added to the backends dict in sigma/cli/backends.py by creation of a Backend named tuple with
the following parameters:
sigma list targets).-f parameter) to descriptions of the formats that are shown in the
format list (sigma list formats <backend>). The formats must be supported by the backend!The dict key is the name used in the -t parameter.
A processing pipeline is defined in the pipelines variable dict in sigma/cli/pipelines.py. The variable contains a
ProcessingPipelineResolver that is instantiated with a dict that maps identifiers that can
be used in the -p parameter to functions that return ProcessingPipeline objects. The descriptive text shown in the pipeline list (sigma list pipelines) is provided from
the name attribute of the ProcessingPipeline object.
The project is currently maintained by:
FAQs
Sigma Command Line Interface (conversion, check etc.) based on pySigma
We found that sigma-cli demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 2 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Product
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.
Product
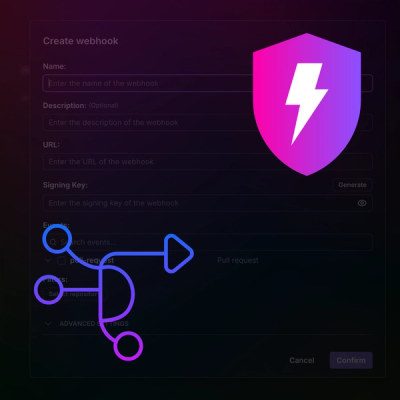
Add real-time Socket webhook events to your workflows to automatically receive pull request scan results and security alerts in real time.

Research
The Socket Threat Research Team uncovered malicious NuGet packages typosquatting the popular Nethereum project to steal wallet keys.