
Security Fundamentals
Turtles, Clams, and Cyber Threat Actors: Shell Usage
The Socket Threat Research Team uncovers how threat actors weaponize shell techniques across npm, PyPI, and Go ecosystems to maintain persistence and exfiltrate data.
A backend for the Toga widget toolkit_ on web platforms.
This package isn't much use by itself; it needs to be combined with the core Toga library_.
For platform requirements, see the Web platform documentation <https://toga.readthedocs.io/en/latest/reference/platforms/web.html#prerequisites>__.
For more details, see the Toga project on Github_.
.. _Toga widget toolkit: https://beeware.org/toga .. _the core Toga library: https://pypi.python.org/pypi/toga-core .. _Toga project on Github: https://github.com/beeware/toga
Toga is part of the BeeWare suite_. You can talk to the community through:
@beeware@fosstodon.org on Mastodon_Discord_Github Discussions forum_We foster a welcoming and respectful community as described in our
BeeWare Community Code of Conduct_.
.. _BeeWare suite: https://beeware.org .. _@beeware@fosstodon.org on Mastodon: https://fosstodon.org/@beeware .. _Discord: https://beeware.org/bee/chat/ .. _Github Discussions forum: https://github.com/beeware/toga/discussions .. _BeeWare Community Code of Conduct: https://beeware.org/community/behavior/
If you experience problems with this backend, log them on GitHub. If you
want to contribute code, please fork the code and submit a pull request_.
.. _log them on Github: https://github.com/beeware/toga/issues .. _fork the code: https://github.com/beeware/toga .. _submit a pull request: https://github.com/beeware/toga/pulls
FAQs
A Web backend for the Toga widget toolkit.
We found that toga-web demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 0 open source maintainers collaborating on the project.
Did you know?

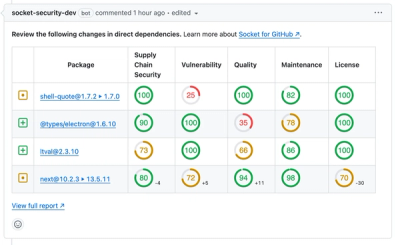
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security Fundamentals
The Socket Threat Research Team uncovers how threat actors weaponize shell techniques across npm, PyPI, and Go ecosystems to maintain persistence and exfiltrate data.

Security News
At VulnCon 2025, NIST scrapped its NVD consortium plans, admitted it can't keep up with CVEs, and outlined automation efforts amid a mounting backlog.
Product
We redesigned our GitHub PR comments to deliver clear, actionable security insights without adding noise to your workflow.