Research
/Security News
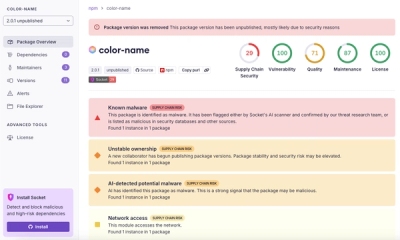
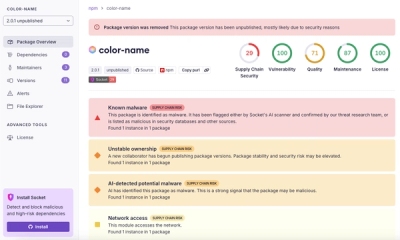
npm Author Qix Compromised via Phishing Email in Major Supply Chain Attack
npm author Qix’s account was compromised, with malicious versions of popular packages like chalk-template, color-convert, and strip-ansi published.
jnunemaker-happymapper
Advanced tools
= happymapper
== DESCRIPTION:
Object to xml mapping library. I have included examples to help get you going. The specs should also point you in the right direction.
== FEATURES:
== EXAMPLES:
Here is a simple example that maps Twitter statuses and users.
class User include HappyMapper
element :id, Integer
element :name, String
element :screen_name, String
element :location, String
element :description, String
element :profile_image_url, String
element :url, String
element :protected, Boolean
element :followers_count, Integer
end
class Status include HappyMapper
element :id, Integer
element :text, String
element :created_at, Time
element :source, String
element :truncated, Boolean
element :in_reply_to_status_id, Integer
element :in_reply_to_user_id, Integer
element :favorited, Boolean
has_one :user, User
end
See examples directory in the gem for more examples.
http://github.com/jnunemaker/happymapper/tree/master/examples/
== INSTALL:
== TICKETS:
http://github.com/jnunemaker/happymapper/issues/
== DOCS:
FAQs
Unknown package
We found that jnunemaker-happymapper demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Research
/Security News
npm author Qix’s account was compromised, with malicious versions of popular packages like chalk-template, color-convert, and strip-ansi published.

Research
Four npm packages disguised as cryptographic tools steal developer credentials and send them to attacker-controlled Telegram infrastructure.

Security News
Ruby maintainers from Bundler and rbenv teams are building rv to bring Python uv's speed and unified tooling approach to Ruby development.