
Security News
Feross on Risky Business Weekly Podcast: npm’s Ongoing Supply Chain Attacks
Socket CEO Feross Aboukhadijeh joins Risky Business Weekly to unpack recent npm phishing attacks, their limited impact, and the risks if attackers get smarter.
= launchpad
{ }[https://travis-ci.org/andeemarks/launchpad]
}[https://travis-ci.org/andeemarks/launchpad]
[https://github.com/andeemarks/launchpad/blob/master/launchpad-gem-overview.gif]
This gem provides a Ruby interface to access the {Novation Launchpad MK2}[https://global.novationmusic.com/launch/launchpad#] programmatically. The code started life as a clone of {Thomas Jachman's gem}[https://github.com/thomasjachmann/launchpad] and was subsequently updated to handle the MK2 version of the Launchpad. The mapping of buttons and specification of colours completely changed when the MK2 was released, so lots of the original code in these areas has been re-written, but the interaction code is still largely intact.
== More Info
Novation's Launchpad MK2 MIDI programmer's reference {here}[https://global.novationmusic.com/sites/default/files/novation/downloads/10529/launchpad-mk2-programmers-reference-guide_0.pdf] was the sole source for helping me understand how to interact with the Launchpad.
Due to limitations in the Portmidi gem, it's not possible to specify which channel is used to send MIDI messages. As such, all interaction with the Launchpad are done over the default channel 1. This means some workarounds have been needed to access functionality like flash and pulse, which usually require channel 2 messages. All of these workarounds have been implemented via sending {System Exclusive messages}[http://electronicmusic.wikia.com/wiki/System_exclusive] as per the above reference guide.
== Requirements
== Compatibility
The gem is known to be compatible with the following ruby versions:
== Installation
The gem is hosted on RubyGems[https://rubygems.org/], so in order to use it, you're gonna gem install it:
gem install launchpad
== Usage
There are two main entry points:
require 'launchpad/device', providing Launchpad::Device, which handles all the basic input/output stuffrequire 'launchpad/interaction' or just 'launchpad', additionally providing Launchpad::Interaction, which lets you respond to actions (button presses/releases)This is a simple example (only requiring the device for output) that resets the launchpad and then lights the grid button at position 4/4 (from bottom left of 0/0).
require 'launchpad/device'
device = Launchpad::Device.new sleep 1 device.reset_all sleep 1 device.change :grid, :x => 4, :y => 4, :color => 72
This is an interaction example lighting all grid buttons in red when pressed and keeping them lit.
require 'launchpad'
interaction = Launchpad::Interaction.new interaction.response_to(:grid, :down) do |interaction, action| interaction.device.change(:grid, action.merge(:color => 72)) end interaction.response_to(:mixer, :down) do |interaction, action| interaction.stop end
interaction.start
For more details, see the examples. examples/color_picker.rb is the most complex example with interaction.
== To Do
== Copyright
Copyright (c) 2017 Andy Marks. See LICENSE for details.
FAQs
Unknown package
We found that launchpad_mk2 demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Socket CEO Feross Aboukhadijeh joins Risky Business Weekly to unpack recent npm phishing attacks, their limited impact, and the risks if attackers get smarter.

Product
Socket’s new Tier 1 Reachability filters out up to 80% of irrelevant CVEs, so security teams can focus on the vulnerabilities that matter.
Research
/Security News
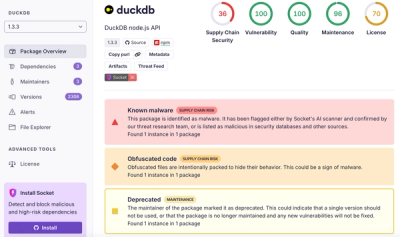
Ongoing npm supply chain attack spreads to DuckDB: multiple packages compromised with the same wallet-drainer malware.