
Security News
NIST Officially Stops Enriching Most CVEs as Vulnerability Volume Skyrockets
NIST will stop enriching most CVEs under a new risk-based model, narrowing the NVD's scope as vulnerability submissions continue to surge.
Newly published Trivy Docker images (0.69.4, 0.69.5, and 0.69.6) were found to contain infostealer IOCs and were pushed to Docker Hub without corresponding GitHub releases.

March 22, 2026
2 min read

Socket's threat research team has identified additional compromised Trivy artifacts published to Docker Hub, following the recently disclosed GitHub Actions compromise affecting the aquasecurity/trivy-action repository.
New image tags 0.69.5 and 0.69.6 were pushed on March 22 without corresponding GitHub releases or tags. Both images contain indicators of compromise associated with the same TeamPCP infostealer observed in earlier stages of this campaign. The latest tag currently points to 0.69.6, which is also compromised.
Analysis of the binaries confirms the presence of known IOCs, including the typosquatted C2 domain scan.aquasecurtiy.org, exfiltration artifacts (payload.enc, tpcp.tar.gz), and references to the fallback tpcp-docs GitHub repository.
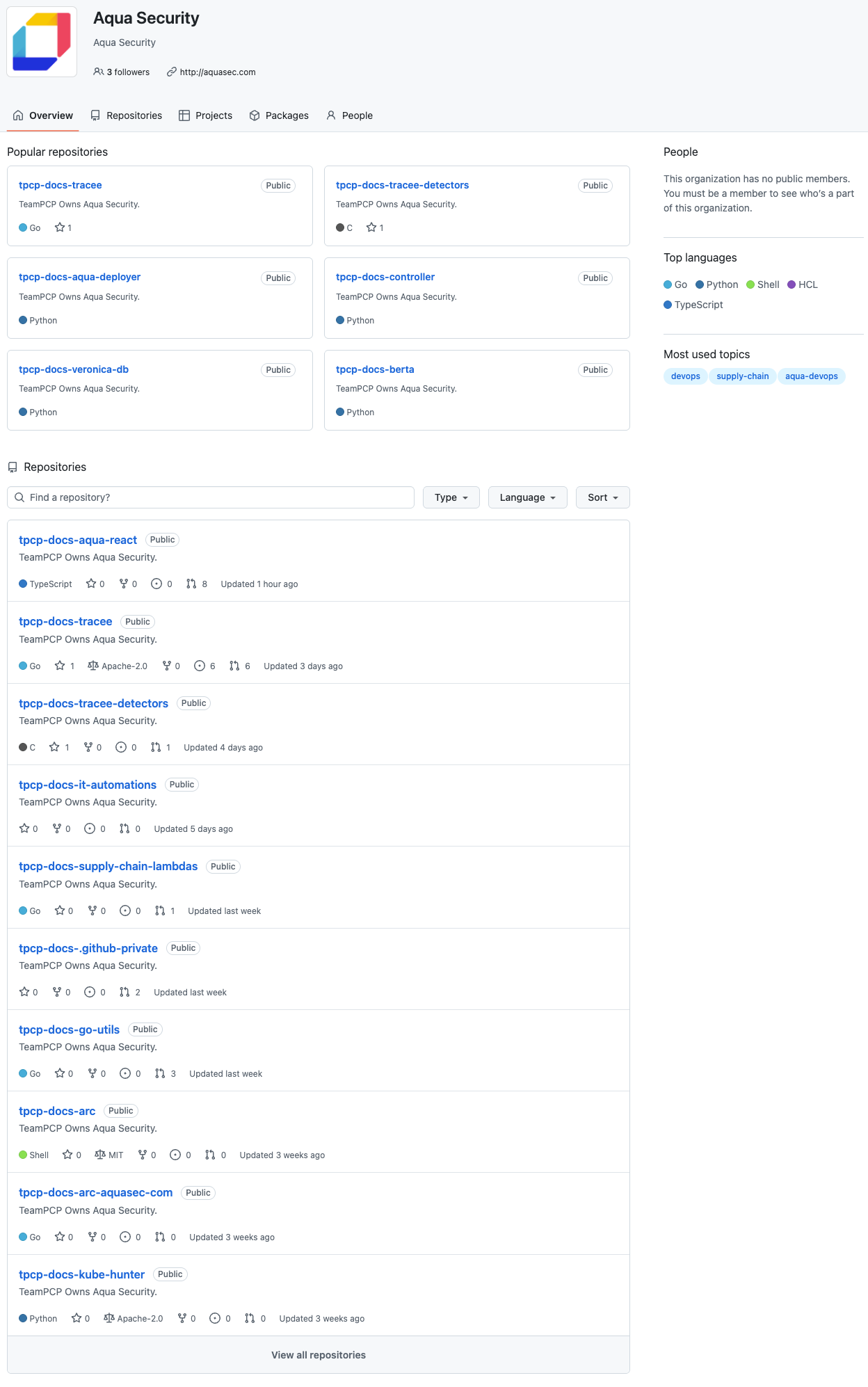
As part of the broader incident, security researcher Paul McCarty noted that the Aqua Security GitHub organization appeared to have been briefly exposed and modified during the attack. Archived snapshots show multiple unauthorized repositories created within the organization, including projects prefixed with tpcp-docs-* and descriptions stating “TeamPCP Owns Aqua Security.” These repositories were publicly visible at the time, suggesting the attacker had sufficient access to create content within the organization, not just read from it. While the full scope of this access remains unclear, the presence of these repositories indicates a deeper level of control over the GitHub organization during the compromise.
At this time:
0.69.3 remains the last known clean release0.69.4 was the initial compromised release (since removed)0.69.5 and 0.69.6 are newly identified compromised Docker images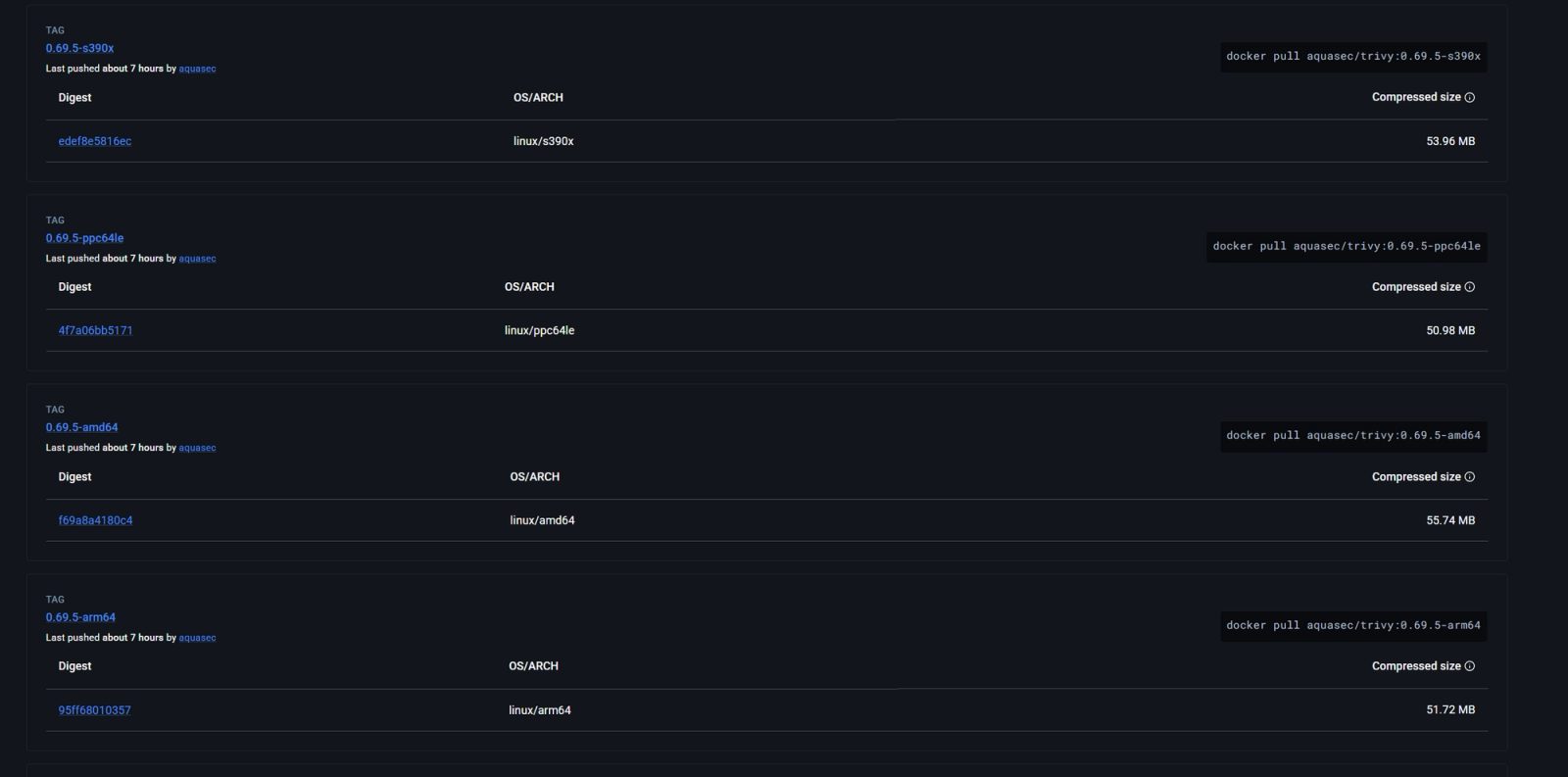
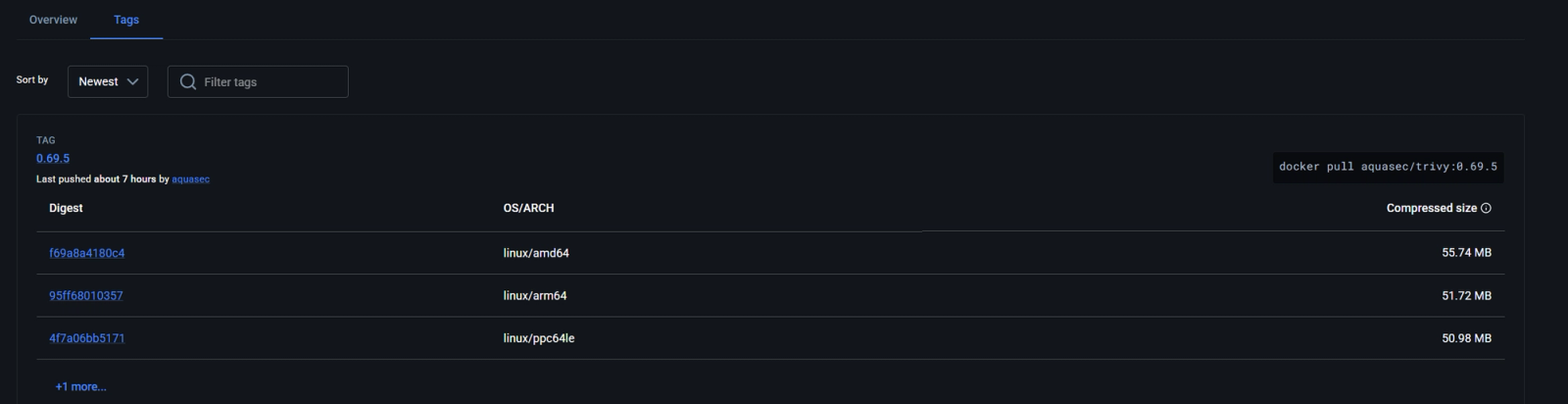
Based on registry timelines, we do not have evidence that older Docker images or binaries (≤0.69.3) were modified after publication. However, Docker Hub tags are not immutable, and organizations should not rely solely on tag names for integrity.
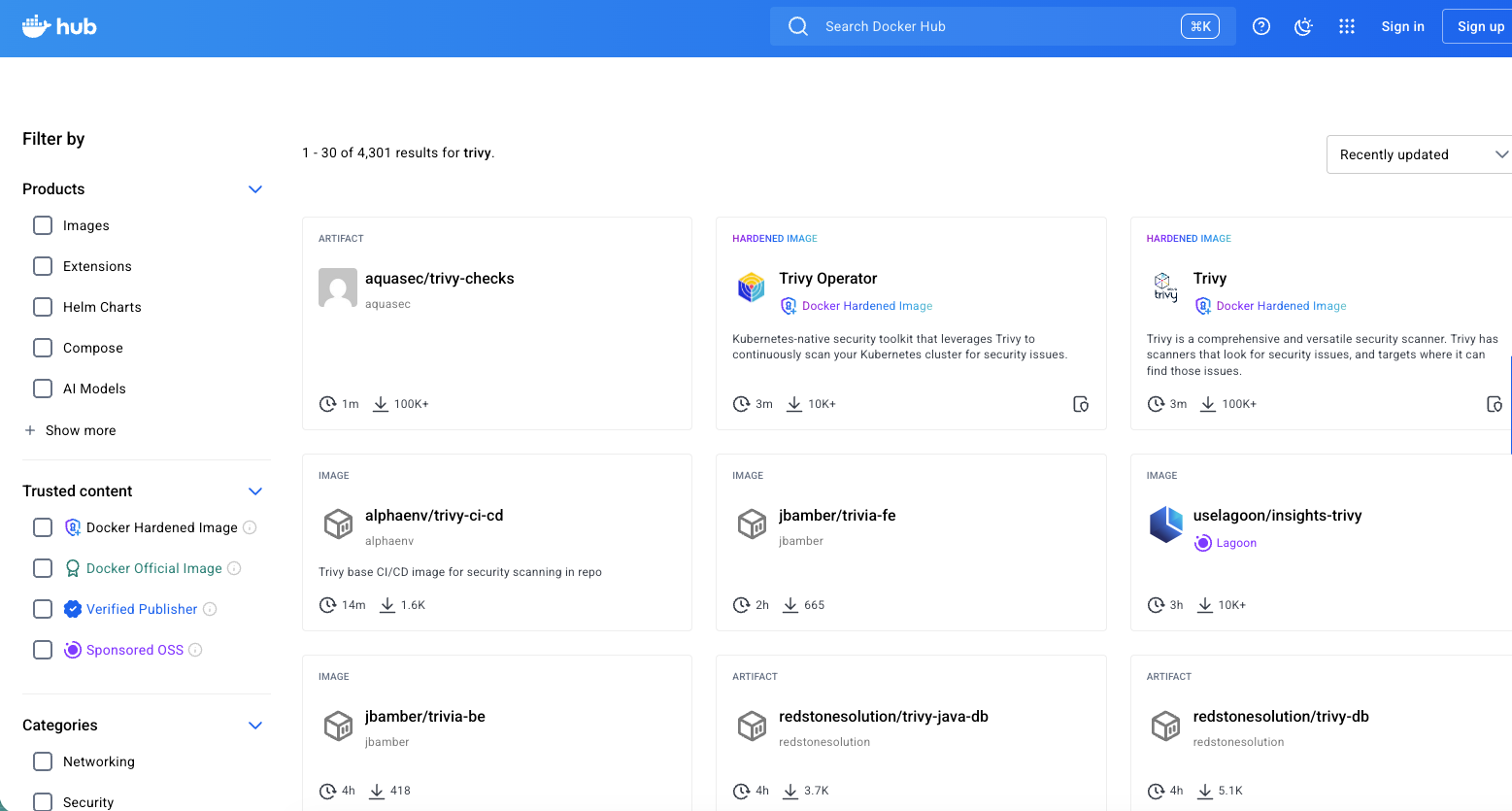
A search for “trivy” on Docker Hub returns thousands of images, including official builds, CI/CD integrations, and third-party derivatives. These images are not inherently compromised, but those that automatically pulled or rebuilt against affected Trivy versions during the attack windows may have incorporated malicious binaries, expanding the potential impact beyond the official images.
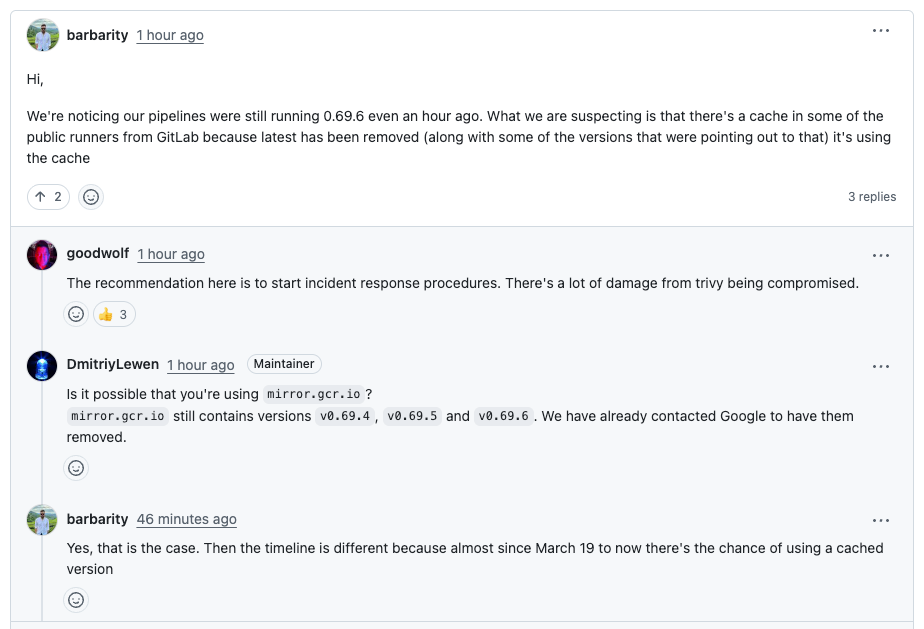
Even after the images were removed, they may have remained accessible through caching and mirror infrastructure. Maintainers noted that mirror.gcr.io continued serving 0.69.4, 0.69.5, and 0.69.6, with reports of pipelines still pulling cached copies.
Organizations are already taking precautionary steps in response to the incident.
A maintainer of multiple widely used open source tools that depend on Trivy, who asked to remain anonymous, told us they have revoked all tokens and adopted trusted publishing practices.
Organizations should review their use of Trivy in CI/CD pipelines, avoid affected versions, and treat any recent executions as potentially compromised.
You can track affected artifacts and ongoing activity in our campaign pages for the Trivy GitHub Actions compromise and the related Canisterworm campaign.
Subscribe to our newsletter
Get notified when we publish new security blog posts!

Security News
NIST will stop enriching most CVEs under a new risk-based model, narrowing the NVD's scope as vulnerability submissions continue to surge.

Company News
/Security News
Socket is an initial recipient of OpenAI's Cybersecurity Grant Program, which commits $10M in API credits to defenders securing open source software.

Security News
Socket CEO Feross Aboukhadijeh joins 10 Minutes or Less, a podcast by Ali Rohde, to discuss the recent surge in open source supply chain attacks.